We’ve talked a bit about reconnaissance, NMAP and SQL Injection. But sometimes, our jobs aren’t strictly limited to demonstrating how vulnerable an application is to known exploits. Sometimes, we get the chance to demonstrate how vulnerable a web application is just by existing.
An administrator or developer can put in defense after defense and make it so we have to jump hoops in order to get to known exploits and that’s good. Defense-in-depth is a great concept and it should be used as a building block of any sound security plan. However, if we can develop an understanding of how an application works well enough (and I mean mind-melding like Spock with that rock creature—you know, the one with the silicon eggs *shudder* ), if we can really get to know an app and understand the code in front of us in a web page, then we should be able to test its security without some of the tools we’ve talked about before.
I’m going to demonstrate how, with the help of a web proxy, we can manipulate an application’s code so much so that we can see information we weren’t supposed to see, gain administrative privileges, even dump a database.
Now, all you critics out there, these are extremely basic examples of how to manipulate javascript and HTML to get us escalated access to data. These are not meant to be elaborate examples, by any means and they aren’t.
But they should serve as a great stepping stone for your education and give you a place to start to learn how to do this.
Ready to begin?
The Web Application
The following examples, while simplistic of nature, are real. They have been found out in the field. I can’t divulge where, but I can divulge how to exploit these loops of logic.
Javascript in the URL bar
Now, there are a couple of different ways to skin this particular cat. Some people would take the resulting URL from this particular manipulation and just copy and paste it into a new browser window and change the URL. This is ordinarily a fine idea. However, SOMEtimes you find a sneaky programmer who has figured out that they need to deny direct URL access if it wasn’t the result of a Javascript call. So, the only way to do this particular trick is by manipulating the javascript that we are given in the first place.
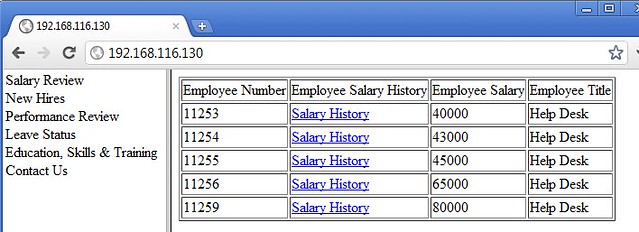
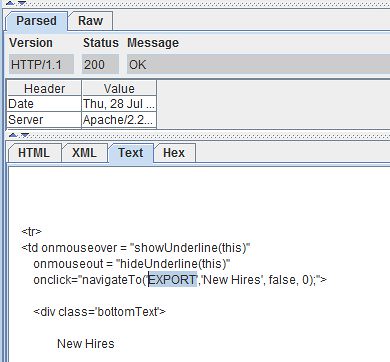
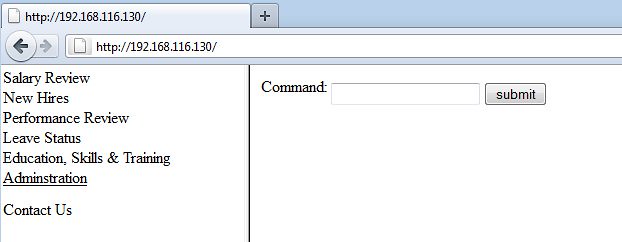
First, we log into our Web Application (a management portal, for this particular example) and we are presented with this screen:
Our menu to the left, shows that we can perform “Salary Review”, look at “New Hires”, execute “Performance Reviews”, take a look at our current employees’ “Leave Status” and review our employees’ “Education, Skills & Training”.
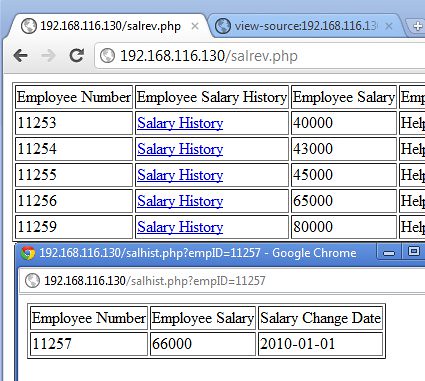
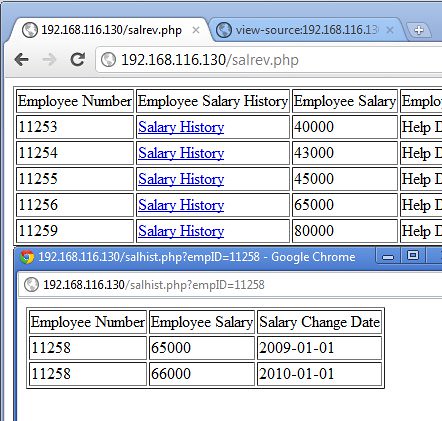
Clicking on “Salary Review”, we are presented with a screen such as this:
This screen shows us a list of the employees we’re in charge of and their current salaries. If we wanted to review a particular employee’s salary history (perhaps we need to know what percentage raise he was given in previous years), we could perform this by click on the “Salary History” link in the right frame.
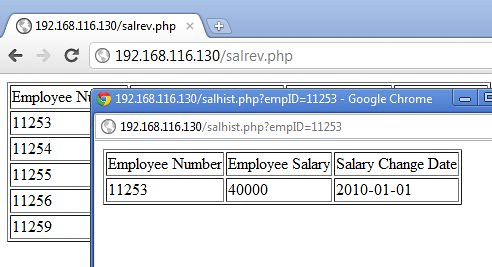
The legitimate results of our doing this would look something like this:
From this, we can see that we clicked the “Salary History” link for employee 11253 and from the window in the background, we can tell that employee 11253 is, indeed, one of our legitimate employees and we SHOULD have the privilege of seeing his salary history.
But we’re supposed to be wearing the darker colored hats of the attacker, aren’t we? So, let’s start to think a bit darker about the information that’s in front of us. We have under us, employees 11253-11256 and an employee with the ID number 11259. So, someone else’s employees are 11257 and 11258. Let’s see how secure our actual program is. Let’s see if we can see information for either employee 57 or 58.
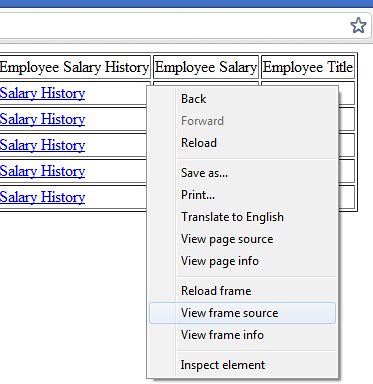
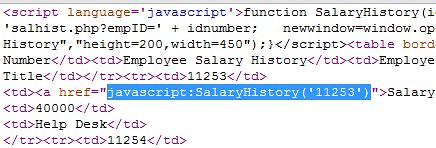
First, let’s take a look at the HTML source code for the page that we’re presented. This is one of the first things I do when interacting with a web application I’m testing. I can’t bend it to my will if I don’t understand what it’s doing.
So, let’s take a look.
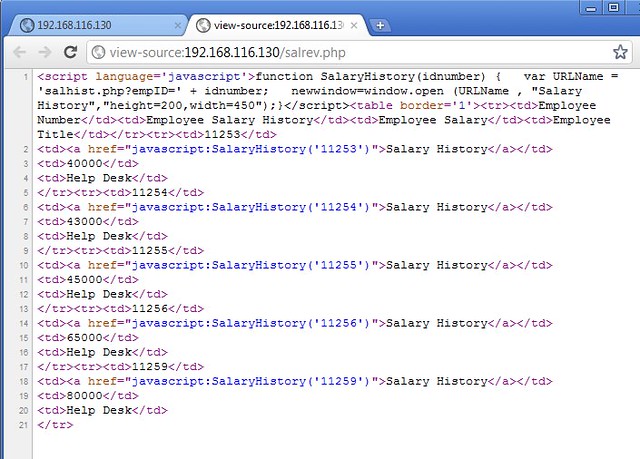
Interestingly, each of our “Salary History” links utilize the same javascript function over and over again. All they do is pass the employee’s ID number along to the function.
The logical question to ask is: “What would happen if I feed this “SalaryHistory()” function the WRONG employee ID number? What would I see?” (Remember, we’re getting paid to think like the bad guys here.
So, we’ll copy “javascript:SalaryHistory(‘11253’)” from the source code and we’re going to use this to manipulate our app around a bit.
Let’s paste this into notepad three times to modify it. Let’s change the second line to reflect the employee ID number 11257 and the third one to reflect the employee ID number 11258.
So, our 3 lines will look like this:
javascript:SalaryHistory(‘11253’)
javascript:SalaryHistory(‘11257’)
javascript:SalaryHistory(‘11258’)
The first thing I always do when puttering around with applications is attempting something legitimate before I try something malign. This way I know that, if the legitimate transaction works, I at least have a better than 50% shot the malign transaction will work, too.
So, let’s paste “javascript:SalaryHistory(‘11253’)” into the URL bar of the application and see where it brings us. If, when you hit enter, you don’t get the right action (a popup box), you might need to open the frame in its own window first. This isn’t always the case, but know you can do it, if necessary.
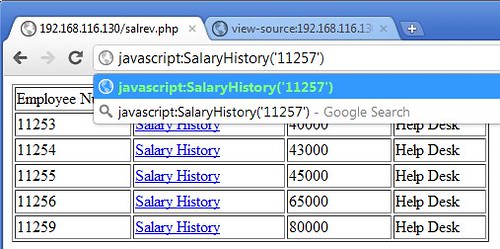
We paste “javascript:SalaryHistory(‘11253’)” and what happens?
Look familiar? It should, it’s the exact same results as if we clicked the link to start with.
OK, now, we’re going to step across the boundary from legitimate application use to the darker hat area.
We’re going to paste the second line from our notepad into the URL bar. We paste “javascript:SalaryHistory(‘11257’)” in.
What happens?
Success!! We’ve successfully gotten the app to return the employee salary history of employee 11257, even though (from the list in the window beneath), he is clearly NOT one of our employees.
And what happens if we do the same with “11258”?
Again, we get their salary history.
While this is basic URL manipulation (in essence), it’s a way to think around a problem that a lot of people skip or miss when evaluating the security of a web application. They rely on automated tools and don’t look beneath the hood to see if there’s anything they can do to mess with the application’s logic.
And that’s a real shame. Why? Because no scanner’s going to figure out that you can glean unauthorized information from the app by manipulating what’s presented to you, the user. And a lot of times, the data that you can gain access to are the crown jewels that you should not be able to see.
Changing the HTML in Front of You
Sometimes, manipulating the code in front of you is not as simple as just changing a couple of characters in a URL bar. Sometimes, you need to actually figure out a way to change the HTML as it’s being fed into your web browser.
This is a perfect situation for using a web proxy. There are several web proxies out there: BurpSuite, WebScarab and Paros to name a few. What is a web proxy and what does it do? Well, to make things incredibly simple: a web proxy is a piece of software that will sit between a web client (a browser) and a web server (http://xxx.xxx.xxx) and will intercept requests from the client and responses from the server. Why does it do this? So that you may manipulate the code in transit to either destination.
It looks a little like this:
And for more detailed information, check out WebScarab’s Getting Started guide on their web
site (https://www.owasp.org/index.php/WebScarab_Getting_Started) and for information on how to set up your web browser to use a proxy, check out this rather complete (f not a tad old) list of browsers and how to change proxy settings. (http://www.cavency.com/browser-proxy.html )
NOTE: One of my favorite ways to use proxies is to use Mozilla Firefox and get the FoxyProxy plugin from their addons.mozilla.org site. FoxyProxy creates a button in the browser window that lets you quickly switch from one proxy to another.
Starting the Web Proxy and Using It
Once you’ve downloaded your particular web proxy (for my examples, I use WebScarab, although it’s a great idea to use a couple and find which one suits your needs and skills best).
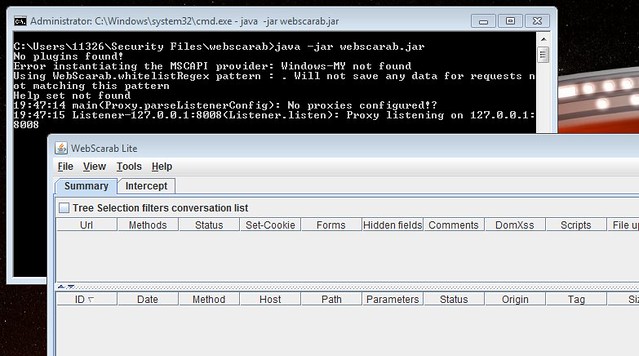
For WebScarab, we need to invoke it using the “java –jar webscarabXXXX.jar” syntax.
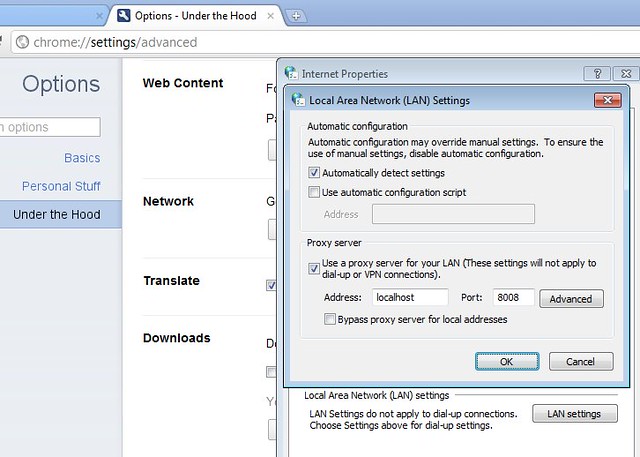
Then, once it’s started (note that in the picture, WebScarab tells you which port it’s running on, port 8008), you’ll need to configure your web browser to use it.
The settings page you’re looking for commonly looks something like this:
Now, every single request from our web browser and response from the server will be processed through this proxy. Later on, we’ll turn on interception and we’ll be able to manipulate the actual HTML as it goes back and forth.
Checking out the Javascript Under the Hood
First, before we do anything else, let’s check out how the application’s navigation menu works. The navigation panel on the left side of the screen is the nuts and bolts of our application. It’s how I, the user, get to places I’m supposed to get around. Chances are, in a security evaluation, this is also a great place for me to find ways to get to places I’m NOT supposed to get around.
So, I’m going to view the source (found here: http://pastebin.com/r7vC3ity ).
Let’s see what’s going on.
The javascript first declares two variables:
var nextAction = "";
Then it declares a function called “navigateTo” and 4 things are passed to it: “screen”, “title”, “rights”, and “timeout”. But the meat of the thing is in the “nextAction = “ line and the “eval(nextAction)”.
function navigateTo(screen, title, rights, timeout){
nextAction = 'navigateTo'+screen+'("'+title+'",'+rights+')';
eval(nextAction);
}
Why are those two lines the meat of the function? Because, whatever we pass to the function in the “screen” variable, it is appended to the phrase “navigateTo”. So, if we were to pass it the phrase “GOOBER”, the nextAction variable would be set to “navigateToGOOBER” and a bunch of extra stuff.
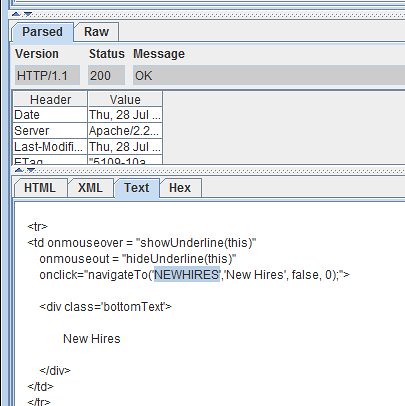
So, that means that down below, where the app’s HTML says:
<tr>
<td onmouseover = "showUnderline(this)"
onmouseout = "hideUnderline(this)"
onclick="navigateTo('NEWHIRES','New Hires', false, 0);">
<div class='bottomText'>
New Hires
</div>
</td>
</tr>
What is really happening, is when we click on the words “New Hires”, the “onClick=” event passes the navigateTo function the following things 'NEWHIRES', 'New Hires', false, and 0. Most of this is irrelevant. However when we pass the “navigateTo” function the phrase “NEWHIRES”, what ends up happening?
“nextAction” becomes “navigateToNEWHIRES”.
And then the code executes the “eval(navigateToNEWHIRES”…blah-blah-blah code.
This in turn executes this code:
function navigateToNEWHIRES(Title, BrowseOnly) {
parent.frameB.location.href = "NEWHIRES.htm"
}
Which means that it redirects the code to NEWHIRES.htm in the long run.
So now we better understand how the navigate menu moves us, the user, around the application.
Now.
How can we break it? Let’s don our darker hat.
The rest of the code actually gives a few clues as to some mischief we can get into. When reviewing all the “navigateToXXXXXX” functions, there are few functions that the developer left in the code. Why did they leave it in the code? Probably because the functionality we’re given as a regular user doesn’t use it and maybe it was easier to leave it in. Who knows why? Who cares? It’s in there and we might get some use out of it.
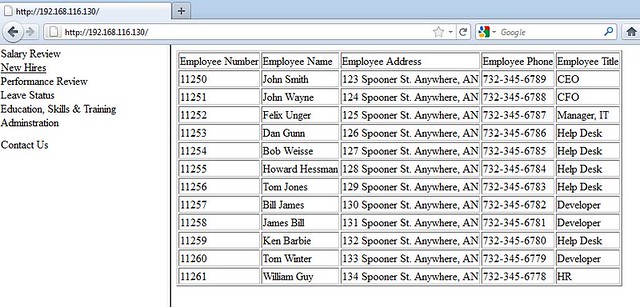
One thing that stands out at me in a big way is the “navigateTOEXPORT” function. Sounds like something we should check out. (And yes, naysayers, we COULD just navigate to export1.php, however, there could be code that blocks a direct reference. This way, we’re using the native functionality of the application against itself).
Let’s see what we can do with the “navigateTOEXPORT” function.
Manipulating the Javascript
So, we talked before about using a web proxy and how it can intercept traffic between a web client or browser and a web server. The reason we discussed it is that we’ve got some code we want to execute (“navigateTOEXPORT”) and the best way to handle that natively is to get one of our EXISTING navigation buttons (let’s say “NEW HIRES”) and change how that button functions.
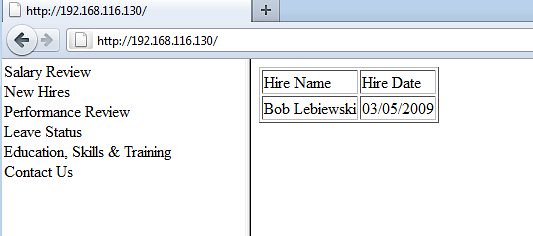
First, let’s see how the NEWHIRES code works normally. By click on the Navigation Menu item marked “New Hires”, we see that we only have 1 record returned back to us:”Bob Lebiewski”. He is a new hire.
So, what we’re going to do is change how the “New Hires” button works. We’re going to fake out the application and make this button now invoke the EXPORT function. This way we’ll see if we can gain unauthorized access to the database export functions.
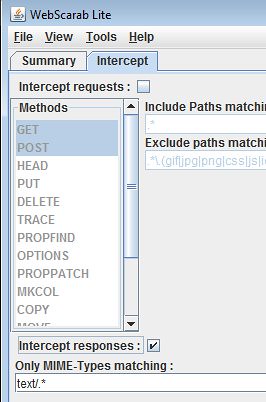
In order to start, we’re going to go into WebScarab and check off the “Intercept Responses” checkbox. This means that what we’re going to do is change the HTML code we render in the browser.
Now, when we refresh the screen, the request will pass through the proxy and because we’ve told WebScarab to intercept server responses, we see the response in a new window. Scrolling down that window, we come to the actual response and can click on the TEXT tab to view and edit the raw HTML.
And we’re going to go ahead and modify the phrase “navigateTo(‘NEWHIRES” to “navigateTo(‘EXPORT”. Why are we doing this? Well, we certainly could copy and paste the entire <tr> clause and modify the whole thing. But, here’s the thing. We want to do this quick and lazy. If we can gain access to the EXPORT function without a lot of work (and let’s face it, 6 keystrokes is quick and easy), then this is the quickest way to go.
So, now we’ve changed the HTML to reflect that our “New Hires” menu button won’t take us all the way to NEWHIRES. It will in fact, when clicked, bring us to the EXPORT function. Hit the “Accept Changes” button on our proxy and we should get a new Navigation Menu that looks exactly like our last one.
Let’s take a look and see what happens when we click it.
It looks like we got a dump of the entire database to the screen. I’d say that’s a win. Was there an authorization check for that web page? Did it check to see if my user account could access it? No. The programmer relied on the fact that my role in the application wasn’t supposed to get the menu item for database export and that was good enough. Clearly it wasn’t.
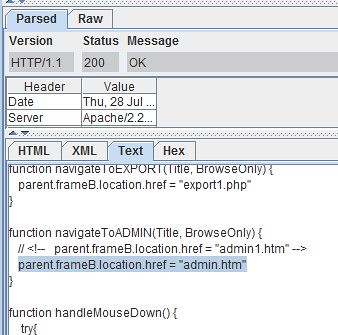
Gaining Unauthorized Access to Admin Functions
Same drill as before. We want to gain access to admin functionality and we’re not admin. The programmer left the code in the HTML for it but thought we, as regular users, were too insignificant to worry about.
Let’s look at that code:
function navigateToADMIN(Title, BrowseOnly) {
parent.frameB.location.href = "admin1.htm"
// <!-- parent.frameB.location.href = "admin.htm" -->
}
So, there’s a comment in the code that redirects us instead to “admin.htm”, rather than “admin1.htm”, the page we’re presented to ordinarily. Again, simple URL manipulation can probably get us where we want to go. But this is a lesson on how to use the Application’s javascript against itself.
Let’s see how the ADMIN function behaves normally.
Admin-access-denied.jpg
Access denied. Interesting.
Now, let’s send this traffic through the proxy and change it up a bit.
First, we see the ADMIN code as is (meaning, the live, uncommented link is to “admin1.htm”).
And with our changes put into the proxy, we have implemented the commented line as our new live link and commented out the “admin1.htm” link.
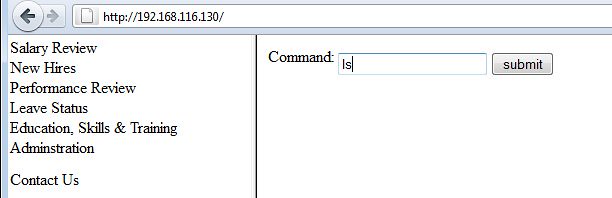
Let’s see what happens when we use the “Administration” button now.
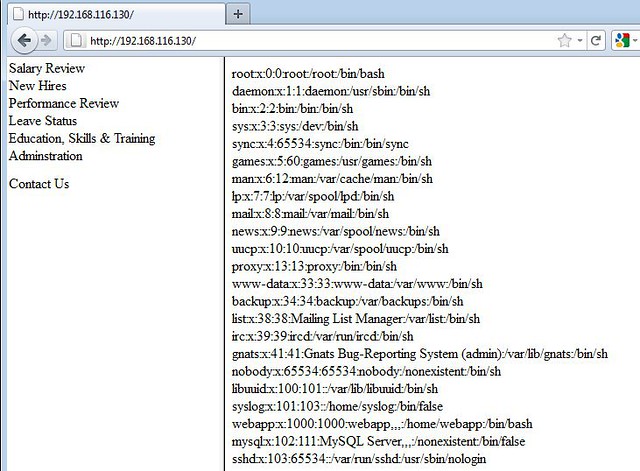
Well, our access is no longer denied. And weird enough, we are presented with a Command text box. What happens when we put “ls” into that box and hit “submit”?
Well, it looks like we’ve gotten into a way to enter commands into the Operating System. That should really just be for administrators. Not regular users like us.
I mean, we could really do some interesting things. Like this:
Conclusion
As stated at the beginning of this article, there are many ways to skin a cat. I wanted to demonstrate for you a quick way to manipulate javascript in a web page to circumvent certain pieces of logic that a developer may have put in place to deter us. By using a web proxy to change the HTML coming into our browser, can alter the application’s behavior and give ourselves access to parts of the application we probably should not have access to.
Hopefully this small demonstration helped get your feet wet with using a proxy and manipulating HTML / Javascript in your browser and playing with web applications and how they behave.
Want to try any of this on your own?
Grab yourself a Virtual Machine that’s already built for LAMP (Linux, Apache, mysql and PHP). There’s one here you might try: http://www.vmware.com/appliances/directory/54966
And then grab yourself this tar file (https://sites.google.com/site/hackonadime/home/files/webapp.tar?attredirects=0&d=1) and untar it in the /var/www directory of your LAMP server. You will have the vulnerable web application we browbeat in this article for your own mischief and mayhem.
Have fun!




My Dad gave me fifa 16 coins hack on my this birthday.
ReplyDeleteHey Guys !
DeleteUSA Fresh & Verified SSN Leads AVAILABLE with best connectivity
All Leads have genuine & valid information
**HEADERS IN LEADS**
First Name | Last Name | SSN | Dob | DL Number |Address | State | City | Zip | Phone Number | Account Number | Bank Name
*Price for SSN lead $2
*You can ask for sample before any deal
*If anyone buy in bulk, we can negotiate
*Sampling is just for serious buyers
==>ACTIVE & FRESH CC FULLZ ALSO AVAILABLE<==
->$5 PER EACH
->Hope for the long term deal
->Interested buyers will be welcome
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
Hello Everyone !
DeleteUSA SSN Leads/Fullz available, along with Driving License/ID Number with good connectivity.
All SSN's are Tested & Verified.
**DETAILS IN LEADS/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL
->EMPLOYEE DETAILS
*Price for SSN lead $2
*You can ask for sample before any deal
*If you buy in bulk, will give you discount
*Sampling is just for serious buyers
->Hope for the long term business
->You can buy for your specific states too
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
SSN FULLZ AVAILABLE
DeleteFresh & valid spammed USA SSN+Dob Leads with DL available in bulk.
>>1$ each SSN+DOB
>>3$ each with SSN+DOB+DL
>>5$ each for premium fullz (700+ credit score with replacement guarantee)
Prices are negotiable in bulk order
Serious buyer contact me no time wasters please
Bulk order will be preferable
CONTACT
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
OTHER STUFF YOU CAN GET
SSN+DOB Fullz
CC's with CVV's (vbv & non-vbv)
USA Photo ID'S (Front & back)
All type of tutorials available
(Carding, spamming, hacking, scam page, Cash outs, dumps cash outs)
SQL Injector
Premium Accounts (Netflix, Pornhub, etc)
Paypal Logins
Bitcoin Cracker
SMTP Linux Root
DUMPS with pins track 1 and 2
WU & Bank transfers
Socks, rdp's, vpn
Php mailer
Server I.P's
HQ Emails with passwords
All types of tools & tutorials.. & much more
Looking for long term business
For trust full vendor, feel free to contact
CONTACT
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
yesterday i was looking for a site that really gives us free playstation codes rather than just show the bullshit.
ReplyDeleteI’ve been attempting for some time possessing said that i in no way ever handle to arrive there!
ReplyDeleteitunes gift card code generator
clash royale cheats apk
Getting free xbox live gold membership code is hardly difficult to do, you should just finish the patron offers without really being forced to spend something, then the code is likely to be given to you.
ReplyDeleteINSTEAD OF GETTING A LOAN, CHECK OUT THE BLANK ATM CARD IN LESS THAN 24hours {blankatmhaker@gmail.com}
ReplyDeleteAm Mark Oscar,I want to testify about Jack Robert blank ATM cards which can withdraw money from any ATM machines around the world. I was very poor before and have no hope then I saw so many testimony about how Jack Robert send them the ATM blank card and use it to collect money in any ATM machine and become rich. I also email him and he sent me the blank card. I have use it to get 70,000 dollars. withdraw the maximum of $5,000 daily. Jack Robert is giving out the card just to help the poor. Hack and take money directly from any ATM Machine Vault with the use of ATM Programmed Card which runs in automatic mode. email Him on how to get it now via: blankatmhaker@gmail.com or call/Text on +1(406) 350-4986
Do you need to increase your credit score?
ReplyDeleteDo you intend to upgrade your school grade?
Do you want to hack your cheating spouse Email, whatsapp, Facebook, instagram or any social network?
Do you need any information concerning any database.
Do you need to retrieve deleted files?
Do you need to clear your criminal records or DMV?
Do you want to remove any site or link from any blog?
you should contact this hacker, he is reliable and good at the hack jobs..
contact : cybergoldenhacker at gmail dot com
Hey Guys !
ReplyDeleteUSA Fresh & Verified SSN Leads AVAILABLE with best connectivity
All Leads have genuine & valid information
**HEADERS IN LEADS**
First Name | Last Name | SSN | Dob | DL Number |Address | State | City | Zip | Phone Number | Account Number | Bank Name
*Price for SSN lead $2
*You can ask for sample before any deal
*If anyone buy in bulk, we can negotiate
*Sampling is just for serious buyers
==>ACTIVE & FRESH CC FULLZ ALSO AVAILABLE<==
->$5 PER EACH
->Hope for the long term deal
->Interested buyers will be welcome
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
Hello Everyone !
ReplyDeleteUSA SSN Leads/Fullz available, along with Driving License/ID Number with good connectivity.
All SSN's are Tested & Verified.
**DETAILS IN LEADS/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL
->EMPLOYEE DETAILS
*Price for SSN lead $2
*You can ask for sample before any deal
*If you buy in bulk, will give you discount
*Sampling is just for serious buyers
->Hope for the long term business
->You can buy for your specific states too
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
Hello everyone 2years back I had $64,000 in debt, including $22,340 in credit card debt. My credit score was nothing to write home about. I managed to get most of my debt removed in bankruptcy and I was left with $8,000 car loan and $35,000 in student loans. I determined not to repeat my mistakes again I was recommended by a credit agency to contact a credit film who would help fix my credit and clear my loans she then referred me to this credit company called Rapid Credit Repairs she has been working with years ago who specializes in fixing credit report. I contacted them through their mail RAPIDCREDITREPAIRS@GMAIL.COM text +1 (415) 754 7204 they got a little info from me and started from raising my credit score to 790 after which they cleared my outstanding pending bills. I bounced back quickly; I am currently on my feet and on my way to buy a house. Thanks so much RAPID CREDIT REPAIRS you guys are simply the best
ReplyDeleteMy name is Andrew Walker, I don’t have much to say but am here to thank TROVIAN CREDIT REPAIRS which i got their contact after visiting my sister and her family and told them my situation at hand how i was knocked out of my home because I was unable to renew rent and my credit profile was messed up in the past. They recommend Trovians to me how they are good in fixing credit, so i contacted them and told them if it’s possible to fix my credit report that has been messed up they gave me a positive answer and they went ahead with the job. In less than 5days my score was raised from a low 478 to 805 excellent and they cleared the eviction, collections late payment. Am happily living well in my new home. I will also recommend you out there to contact them now via email (TROVIANCREDITREPAIR@GMAIL.COM +1 505 926 3648) for your credit repairs services.
ReplyDeleteMy name is Hibbert Davidson, I’m so delighted because I never believed I could get rid of the negative items (Eviction, collections, late payments, medical bills and student loan) recorded on my credit report. Couple of months ago I contacted some credit repair company (Lexington law, online impostors) after paying a nonrefundable deposit service charge, they could barely delete any items from my credit report. I became troubled and decided to express my feelings to my colleague at work who referred me to a credit expert called HACKNET I contacted him on HACKNET567@GMAIL.COM/ 949 397 8437. I explained my problems to him and I gave him a try and the job was done neatly, he raised my credit score to a high 820 now I can apply for anything. He can fix Chex system and a DUI report as well. I believe most of you have credit issues and would probably consider this opportunity.
ReplyDeleteI Want to use this medium to appreciate an online ghost hacker, after being ripped off my money he helped me find my cheating lover and helped me hacked his WHATSAPP, GMAIL, kik and all his social media platforms and i got to know that he has being cheating on me and in less than 24 hours he helped me out with everything, hacking setting is trust worthy, contact him via: hackingsetting50@gmail.com
ReplyDeleteI Want to use this medium to appreciate an online ghost hacker, after being ripped off my money he helped me find my cheating lover and helped me hacked his WHATSAPP, GMAIL, kik and all his social media platforms and i got to know that he has being cheating on me and in less than 24 hours he helped me out with everything, hacking setting is trust worthy, contact him via: hackingsetting50@gmail.com
ReplyDeleteSelling USA FRESH SPAMMED SSN Leads/Fullz, along with Driving License/ID Number with EXCELLENT connectivity.
ReplyDelete**PRICE**
>>2$ FOR EACH LEAD/FULLZ/PROFILE
>>5$ FOR EACH PREMIUM LEAD/FULLZ/PROFILE
**DETAILS IN EACH LEAD/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER WITH EXPIRY DATE
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL, I.P ADDRESS
->EMPLOYEE DETAILS
->REALTIONSHIP DETAILS
->MORTGAGE INFO
->BANK ACCOUNT DETAILS
>All Leads are Tested & Verified.
>Invalid info found, will be replaced.
>Serious buyers will be welcome & I will give discounts for bulk orders.
>Fresh spammed data of USA Credit Bureau
>Good credit Scores, 700 minimum scores
>Bulk order will be preferable
>Minimum order 20 leads/fullz
>Hope for the long term business
>You can asked for samples, specific states & zips (if needed)
>Payment mode BTC, PAYPAL & PERFECT MONEY
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
''OTHER GADGETS PROVIDING''
>Dead Fullz
>Carding Tutorials
>Hacking Tutorials
>SMTP Linux Root
>DUMPS with pins track 1 and 2
>Sock Tools
>Server I.P's
>USA emails with passwords (bulk order preferable)
**Contact 24/7**
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
**SELLING SSN+DOB FULLZ**
ReplyDeleteCONTACT 24/7
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
>>1$ each without DL/ID number
>>2$ each with DL
>>5$ each for premium (also included relative info)
Price will be reduce in Bulk order
FORMAT OF LEADS/FULLZ/PROS
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER WITH EXPIRY DATE
->COMPLETE ADDRESS
->PHONE NUMBER, EMAIL, I.P ADDRESS
->EMPLOYMENT DETAILS
->REALTIONSHIP DETAILS
->MORTGAGE INFO
->BANK ACCOUNT DETAILS
>All Leads are Spammed & Verified.
>Fresh spammed data of USA Credit Bureau
>Good credit Scores, 700 minimum scores
>Invalid info found, will be replaced.
>Payment mode BTC, ETH, LTC, PayPal, USDT & PERFECT MONEY
''OTHER GADGETS PROVIDING''
>SSN+DOB Fullz
>CC with CVV
>Photo ID's
>Dead Fullz
>Carding Tutorials
>Hacking Tutorials
>SMTP Linux Root
>DUMPS with pins track 1 and 2
>Sock Tools
>Server I.P's
>HQ Emails with passwords
Contact 24/7
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
El software de gestión de seguridad es muy importante en la gestión de incidentes, las investigaciones
ReplyDeleteSSN FULLZ AVAILABLE
ReplyDeleteFresh & valid spammed USA SSN+Dob Leads with DL available in bulk.
>>1$ each SSN+DOB
>>3$ each with SSN+DOB+DL
>>5$ each for premium fullz (700+ credit score with replacement guarantee)
Prices are negotiable in bulk order
Serious buyer contact me no time wasters please
Bulk order will be preferable
CONTACT
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
OTHER STUFF YOU CAN GET
SSN+DOB Fullz
CC's with CVV's (vbv & non-vbv)
USA Photo ID'S (Front & back)
All type of tutorials available
(Carding, spamming, hacking, scam page, Cash outs, dumps cash outs)
SQL Injector
Premium Accounts (Netflix, Pornhub, etc)
Paypal Logins
Bitcoin Cracker
SMTP Linux Root
DUMPS with pins track 1 and 2
WU & Bank transfers
Socks, rdp's, vpn
Php mailer
Server I.P's
HQ Emails with passwords
All types of tools & tutorials.. & much more
Looking for long term business
For trust full vendor, feel free to contact
CONTACT
Telegram > @leadsupplier
ICQ > 752822040
Email > leads.sellers1212@gmail.com
==>Contact 24/7<==
ReplyDelete**Telegram > @leadsupplier
**ICQ > 752822040
**Skype > Peeterhacks
**Wickr me > peeterhacks
**SSN FULLZ WITH HIGH CREDIT SCORES AVAILABLE**
>For tax filling/return
>SSN dob DL all info included
>For SBA & PUA filling
>Fresh spammed & Fresh database
**TOOLS & TUTORIALS AVAILABLE FOR HACKING SPAMMING CARDING CASHOUTS CLONING**
FRESHLY SPAMMED
VALID INFO WITH VALID DL EXPIRIES
*SSN Fullz All info included*
NAME+SSN+DOB+DL+DL-STATE+ADDRESS
Employee & Bank details included
CC & CVV'S ONLY USA AVAILABLE
SSN+DOB
SSN+DOB+DL
High credit fullz 700+
(bulk order negotiable)
*Payment in all crypto currencies will be accepted
->You can buy few for testing
->Invalid info found, will be replaced
->Serious buyers contact me for long term business & excellent profit
->Genuine & Verified stuff
TOOLS & TUTORIALS Available For:
(Carding, spamming, hacking, scripting, scam page, Cash outs, dumps cash outs)
=>Ethical Hacking Tools & Tutorials
=>Kali linux
=>Facebook & Google hacking
=>Bitcoin Hacking
=>Bitcoin Flasher
=>SQL Injector
=>Bitcoin flasher
=>Viruses
=>Keylogger & Keystroke Logger
=>Logins Premium (Netflix, coinbase, FedEx, PayPal, Amazon, Banks etc)
=>Bulk SMS Sender
=>Bitcoin Cracker
=>SMTP Linux Root
=>DUMPS track 1 and 2 with & without pin
=>Smtp's, Safe Socks, rdp's, VPN, Viruses
=>Cpanel
=>PHP mailer
=>Server I.P's & Proxies
=>HQ Emails Combo (Gmail, yahoo, Hotmail, MSN, AOL, etc)
->Serious buyers are always welcome
->Big discount in bulk order
->Discounted Offers will give time to time
->Hope we do a great business together
==>Contact 24/7<==
**Telegram > @leadsupplier
**ICQ > 752822040
**Skype > Peeterhacks
**Wickr me > peeterhacks
I am impressed by the way the article is written. Please share some more ideas in this article. Keep me updated in this article. Now its time to avail boise airport shuttle for more information.
ReplyDelete🚨🚨 YOU EVER GOT SCAMMED, THEN YOU SHOULD READ THIS 🚨🚨🚨
ReplyDeleteYou could probably get your money back, and I said probably, This is because most scammers don't move the money to a bank account, most scammers move it to a crypto currency wallet or a local money saving platforms, this way they stay undetected and noticed by authorities.
What you have to keep in mind is, this crypto wallet can be reported or hacked into, and this is what we do.
WHO ARE WE⁉️ YOU MIGHT ASK❗❕❗❕
We are ⭐PYTHONAX⭐ a group of skilled and experienced internet and computer experts. We have refocused our work force into tracking down scammers and helping victims of scam recover their money, or what's left of it. Using our experience in transactions tracking and jail breaking, we can now guarantee scam victims an opportunity to recover their money.
There are so many ways to get scammed in the world we live in today, majority of this scams are internet based scam, one of the major disadvantages of the internet. Here are examples of scams we have dealt with and can help such victims to this scams as well-:
❌Cryptocurrency investments scammed victims.
❌Forex/Binary Option investments scam victims.
❌Buying and Selling scam victims.
❌Dating & Romance scam victims.
❌Loans scams victims.
❌Housing & Estate Investments Scam victims. E.t.c.
How services are simple and and a breakdown of each steps of the process we will take to help you get your money back would be explained and told to you, what we do isn't illegal, we try and follow the rules and make sure you aren't involved in any crime. You can choose to remain anonymous, your personal info wouldn't be required of you, all we need are infos regarding the scam, infos like-:
1️⃣ Total Amount of what you were scammed.
2️⃣ The type of scam you were involved in.
3️⃣ The means of Communication you used in communicating with the scammers. Eg, emails, numbers or social media handles......
4️⃣ Details of which you used to make payments and transactions ID.
Do not feel shy or ashamed or stupid, this scammers are really good at what they do, they make everything look so real and convince and very very real like the actual real stuff.
Use this emails below to contact us-:
PYTHONAXHELP@PROTONMAIL.COM
PYTHONAXSERVICES@PROTONMAIL.COM
We assure you of no form of judgmets or guilt, we are professionals and only want to help.